Chapter Phar 7 - docs.legis.wisconsin.gov
Note: Chapter Phar 7 as it existed on December 31, 2020, was repealed and a new chapter Phar 7 was created, effective January 1, 2021. Subchapter I — General Phar 7.01 Definitions. In this chapter: (1) “Control number” means a unique number used to identify a repackaged drug or drug product in reference to a record that
Download Chapter Phar 7 - docs.legis.wisconsin.gov
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Chapter SPS 382 - Wisconsin
docs.legis.wisconsin.govPublished under s. 35.93, Wis. Stats., by the Legislative Reference Bureau. is the date the chapter was last published. (4)
Chapter DHS 83 - Wisconsin Legislative Documents
docs.legis.wisconsin.govDHS 83.02 WISCONSIN ADMINISTRATIVE CODE 148 Published under s. 35.93, Wis. Stats., by the Legislative Reference Bureau. Published under s. 35.93, Stats.
Chapter SPS 316 - Wisconsin
docs.legis.wisconsin.govSPS 316.002 WISCONSIN ADMINISTRATIVE CODE 196 Published under s. 35.93, Wis. Stats., by the Legislative Reference Bureau. Published under s. 35.93, Stats.
Chapter SPS 321 - Wisconsin
docs.legis.wisconsin.gov19 SAFETY AND PROFESSIONAL SERVICES SPS 321.02 Published under s. 35.93, Stats. Updated on the first day of each month. Entire code is always current.
Chapter A−E 13 - Wisconsin Legislative Documents
docs.legis.wisconsin.govply with the continuing education requirements for the first renewal of registration. (b) ... education requirements under this chapter, including a certificate
Education, Requirements, Chapter, Wisconsin, Continuing, Education requirements, Continuing education requirements for
Chapter MPSW 19 - Wisconsin
docs.legis.wisconsin.govChapter MPSW 19 CONTINUING EDUCATION ... a credential holder who fails to meet the continuing education requirements by the renewal deadline must discontinue
Education, Requirements, Chapter, Wisconsin, Continuing, Continuing education requirements, Chapter mpsw 19, Mpsw, Chapter mpsw 19 continuing education
Chapter SPS 382 - Wisconsin
docs.legis.wisconsin.govSPS 382 Appendix WISCONSIN ADMINISTRATIVE CODE 86 Published under s. 35.93, Wis. Stats., by the Legislative Reference Bureau. Published under s. 35.93, Stats.
Chapter NR 45 - Wisconsin
docs.legis.wisconsin.govchapter NR 45 was created effective January 1, 1984. NR 45.01 Purpose. The purpose of this chapter is to gov-ern the conduct of visitors to state lands and to provide ...
CHAPTER 346
docs.legis.wisconsin.govCHAPTER 346 RULES OF THE ROAD SUBCHAPTER I GENERAL PROVISIONS 346.01 Words and phrases defined. 346.02 Applicability of chapter. 346.03 Applicability of rules of the road to authorized emergency vehicles. 346.04 Obedience to traffic officers, signs and signals; fleeing from officer.
Rules, Road, Chapter, Rules of the road, Chapter 346, Chapter 346 rules of the road
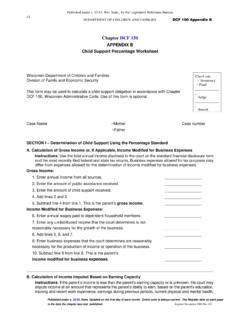
Chapter DCF 150 - docs.legis.wisconsin.gov
docs.legis.wisconsin.govRegister November 2008 No. 635 is the date the chapter was last published. history of child care responsibilities as the parent with primary physical placement, and the availability of work in or near the parent’s community.
Chapter, November, Wisconsin, 2008, Giles, Docs, November 2008, Chapter dcf 150
Related documents
Data Mining - Stanford University
infolab.stanford.edu1.1.3 Computational Approaches to Modeling More recently, computer scientists have looked at data mining as an algorithmic problem. In this case, the model of the data is simply the answer to a complex query about it. For instance, given the set of numbers of Example 1.1, we might compute their average and standard deviation. Note that these ...
Introduction to Computer Security PDF Done
www.uoitc.edu.iqComputer Security Matt Bishop Boston • San Francisco • New York • Toronto • Montreal London • Munich • Paris • Madrid Capetown • Sydney • Tokyo • Singapore • Mexico City Bishop.book Page iii Tuesday, September 28, 2004 1:46 PM
Chapter 2: Patch Management Best Practices - Security
www.windowsecurity.comChapter 2 21 There are a few terms that you need to be aware of as you read through this chapter. Table 2.1 lists the key security terms used in relation to the patch management process. Term Definition Vulnerability Software, hardware, a procedural weakness, a …
Chapter 1: Distributed Systems: What is a distributed system?
www.cs.helsinki.fiIntranets ( CoDoKi, Fig. 1.2) a single authority protected access - a firewall - total isolation may be worldwide typical services: - infrastructure services: file service, name service - application services CoDoKi, Fig. 1.2 Figure 1.2 A typical intranet …
Chapter 12. Database Security - University of Cape Town
www.cs.uct.ac.za• Appreciate the limitations of security subsystems. Introduction In parallel with this chapter, you should read Chapter 19 of Thomas Connolly and Carolyn Begg, “Database Systems A Practical Approach to Design, Imple-mentation, and Management”, (5th edn.). Security is a large subject and one that, because it touches every activity of
Chapter 1 -- An Introduction To Financial Management
www.csun.edu1 Chapter 1 -- An Overview of Financial Management ... A derivative security is a security whose value is derived from the value of an underlying asset. For example, futures contracts and option contracts ... OTC markets are connected by computer network with many dealers and brokers, such as NASDAQ . 10
Chapter 4 Understanding Electronic Health Records, the ...
www.healthit.govThe Security Rule has several types of safeguards and requirements which you must apply: 1. Administrative Safeguards. 52 – Administrative safeguards are administrative actions, policies, and procedures to prevent, detect, contain, and correct security violations. Administrative
Chapter 1 Introduction to Ethical Hacking
www.principlelogic.comChapter 1 Introduction to Ethical Hacking In This Chapter ... ers and network for security vulnerabilities and plugging the holes you find before the bad guys get a chance to exploit them. ... Hackers break into buildings, computer rooms, or other areas containing crit-