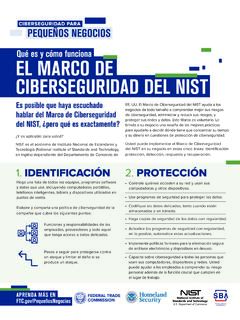
Qué es y cómo funciona EL MARCO DE CIBERSEGURIDAD …
EE. UU. El Marco de Ciberseguridad del NIST ayuda a los negocios de todo tamaño a comprender mejor sus riesgos de ciberseguridad, administrar y reducir sus riesgos, y proteger sus redes y datos. Este Marco es voluntario. Le brinda a su negocio una reseña de las mejores prácticas para ayudarlo a decidir dónde tiene que concentrar su tiempo
Download Qué es y cómo funciona EL MARCO DE CIBERSEGURIDAD …
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Findings of Fact and Conclusions of Law Issued By …
www.ftc.gov3:09-cv-03073-SEM-TSH # 797 Page 1 of 475 E-FILED Monday, 05 June, 2017 02:16:37 PM Clerk, U.S. District Court, ILCD IN THE UNITED STATES DISTRICT COURT
.. It - ftc.gov
www.ftc.govWe respectfully submit that if, as has been suggested, "late night television advertising" is the primary basis for the staff's concern, then the agency already has both the authority and the responsibility to go after
DALLAS REGIONAL OFFICE - ftc.gov
www.ftc.govto improve consumer access to professional services by initiating ... Dallas Regional Office and the Bureau of ... regulations governing architects ...
Professional, Regulations, Office, Regional, Governing, Dallas, Architect, Regulations governing architects, Dallas regional office
Date Certified: MEMORANDUM OF …
www.ftc.govMemorandum of Understanding on the establishment of a joint venture between Alberta Government Services, Canada's Competition Bureau, United States Federal Trade Commission's Bureau of Consumer Protection, Royal Canadian Mounted Police, Calgary Police Service, Edmonton Police Service, and United States Postal Inspection …
Federal, Commission, Understanding, Trade, Memorandum, Canadian, Federal trade commission, Memorandum of understanding, Memorandum of
Final Model Privacy Form Under the Gramm-Leach …
www.ftc.govThis guide was prepared by the staff of the FTC as a “small entity compliance guide” under Section 212 of the Small Business Regulatory Enforcement Fairness Act of …
Form, Guide, Model, Compliance, Entity, Under, Privacy, Small, Final, Small entity compliance guide, Final model privacy form under the gramm, Gramm
for January – December 2016 - Federal Trade …
www.ftc.govConsumer Sentinel Network Complaint Type Percentages. 1 . Calendar Years 2014 through 2016 . Complaint Types. 2 - Identity Theft Complaints - Other Complaints
Federal, Network, 2016, Trade, Consumer, Through, Sentinel, Federal trade, Consumer sentinel network, Through 2016
FTC Staff Guidance on Active Supervision of State ...
www.ftc.govOctober 2015 1 FTC Staff Guidance on Active Supervision of State Regulatory Boards Controlled by Market Participants ∗ I. Introduction . States craft regulatory policy through a variety of actors, including state legislatures,
Analysis Of Agreement Containing Consent Orders …
www.ftc.gov1 . ANALYSIS OF AGREEMENT CONTAINING CONSENT ORDERS . TO AID PUBLIC COMMENT . In the Matter of Abbott Laboratories and St. Jude Medical, Inc. File No. 161 0126, Docket No. C-4600
Analysis, Agreement, Order, Consent, Containing, Jude, Analysis of agreement containing consent orders
ROBIN L. MOORE - Protecting America's Consumers
www.ftc.gov1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 ROBIN L. MOORE FRANK M. GORMAN JAMES A. KOHM Division of Enforcement
THEORY AND PRACTICE OF COMPETITION …
www.ftc.govTHEORY AND PRACTICE OF COMPETITION ADVOCACY AT THE FTC JAMES C. COOPER PAUL A. PAUTLER TODD J. ZYWICKI* This past fall marked the thirtieth anniversary of a pivotal moment in the establishment of the modern competition advocacy program at the FTC, Chairman Lewis Engman’s speech on the
Practices, Competition, Advocacy, Competition advocacy, And practice of competition, And practice of competition advocacy at
Related documents
Cyber Security Framework Saudi Arabian Monetary Authority
sama.gov.saVersion 1.0 Page 6 of 56 Integrity – Information assets are accurate, complete and processed correctly (i.e., protected from unauthorized modification, which may include authenticity and non-repudiation). Availability – Information assets are resilient and accessible when required (i.e., protected from unauthorized disruption).
V20200813 Ingeniería en Ciberseguridad
unicaribe.edu.doinc-402 proyecto de ciberseguridad - ii 5 inc-401 inc-334 ingenierÍa social 3 inc-222 fgc-111 seminario de grado 3 fgc-103 duodÉcimo cuatrimestre clave asignatura cr pre-req inc-414 taller de seguridad iot y entornos industriales 4 inc-333 inc-421 anÁlisis forense en ciberseguridad 4 …
Recopilación Actualizada de Normas Bancos - Capítulo 20-10 …
www.cmfchile.clinformación y ciberseguridad, así como del cumplimiento de sus políticas e incidentes de seguridad de la información y ciberseguridad, con el fin de mejorar su gestión y prevención. - El Directorio ha aprobado políticas de conducta interna, de manera que todos los empleados y/o personas externas que presten servicios a la entidad
NEW YORK STATE DEPARTMENT OF FINANCIAL SERVICES 23 …
www.governor.ny.gov2 (b) Authorized User means any employee, contractor, agent or other Person that participates in the business operations of a Covered Entity and is authorized to access and use any Information Systems and data of the Covered Entity. (c) Covered Entity means any Person operating under or required to operate under a license, registration, charter, certificate, permit, accreditation or …
Guía nacional de notificación y gestión de ciberincidentes
www.incibe-cert.esciberseguridad acaecidos en el seno de las Administraciones Públicas, las infraestructuras críticas y operadores estratégicos de su competencia, así como el resto de entidades comprendidas en el ámbito de aplicación del Real Decreto-Ley 12/2018. Se expone a continuación un esquema orientativo acerca de autoridades competentes ...
Ciberseguridad en el teletrabajo
www.incibe.esC í 7 3 OBJETIVOS DE SEGURIDAD EN EL ACCESO REMOTO Tanto si trabajamos en las instalaciones de la empresa como si teletrabajamos, debemos proteger el principal activo de la organización, la información.La se-
Tecnologías biométricas aplicadas a la ciberseguridad
www.incibe.esTECNOLOGÍAS BIOMTRICAS APLICADAS A LA CIBERSEGURIDAD 3 Una guía de aproximación para el empresario 5. Soluciones biométricas en el catálogo de seguridad de INCIBE 20 6. Beneficios del uso de tecnologías biométricas en la empresa 21 6.1 Para las organizaciones y usuarios finales 21 6.1.1. Aumento de la seguridad en el control de accesos ...