Service Tactics Techniques And Procedures
Found 6 free book(s)BY ORDER OF THE AIR FORCE TACTICS, TECHNIQUES …
static.e-publishing.af.milThe Air Force Tactics, Techniques, and Procedures (AFTTP) 3-42 series of publications is the primary reference for medical operations. AFTTP 3-42.32 provides tactics, techniques and procedures (TTP) for installation medical commanders to plan, prepare, and …
EXPEDITIONARY MEDICAL SUPPORT (EMEDS) AND AIR …
static.e-publishing.af.milPURPOSE: The Air Force Tactics, Techniques, and Procedures (AFTTP) 3-42 series of publications is the primary reference for medical combat support capability. AFTTP 3-42.71 provides the tactics, techniques, and procedures (TTP) for Expeditionary Medical Support (EMEDS) and Air Force Theater Hospital (AFTH) unit type codes (UTCs). Ensure all records
JP 3-13.4, Military Deception - National Defense University
jfsc.ndu.eduMILDEC Means, Tactics, Techniques, and Procedures . MILDEC employs three basic means: physical, technical, and administrative . Employ these means independently or in collaboration depending on the situation. The applications of tactics vary with each operation depending on variables such as time, assets, equipment, and objectives
Tactical Employment of Mortars - United States Marine Corps
www.trngcmd.marines.milCHAPTER 6 - MORTAR PLATOON AND SECTION TACTICS, TECHNIQUES, AND PROCEDURES Section I - Employment Techniques 6-1. Employment by Platoon 6-2. Employment by Section 6-3. Employment by Squad Section II - Reconnaissance, Selection, and Occupation of Mortar Positions 6-4. Definition 6-5. Methods of Reconnaissance 6-6. Planning …
MCRP 3-01B Pistol Marksmanship - United States Marine …
www.marines.milTo be combat ready, a Marine must be skilled in the tactics, techniques, and procedures of pistol marksmanship and diligent in the proper care and maintenance of …
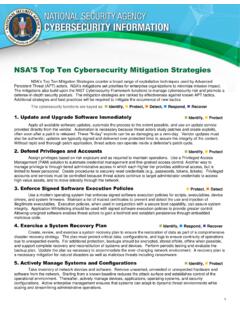
NSA’S Top Ten Cybersecurity Mitigation Strategies
www.nsa.govdefense-in-depth security posture. The mitigation strategies are ranked by effectiveness against known APT tactics. Additional strategies and best practices will be required to mitigate the occurrence of new tactics. The cybersecurity functions are keyed as: Identify, Protect, Detect, Respond, Recover 1.