Incident Reporting - United States Army
higher headquarters to the policy propo- ... or imminent threat of violation of security policies, security procedures, or acceptable use policies. Treat evidence or suspicion of an incident, intrusion, or criminal activity with care, and maintain the IS without change, pending coordination ... (local management device/key processor
Policy, United, States, Devices, Security, Reporting, Army, United states army
Download Incident Reporting - United States Army
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Army Reserve Mission, Organization, and Training
armypubs.army.milArmy Regulation 140–1 Army Reserve Mission, Organization, and Training ... Army Reserve Mission, Organization, and Training ... Area commands • 1–5, page 1
Reserve, Training, Mission, Organization, Army, Pages, Page 1, Training and, Army reserve mission, 1 army reserve mission
INITIATE A TACTICAL COMBAT CASUALTY CARE CARD⁜
armypubs.army.milPlease wait... If this message is not eventually replaced by the proper contents of the document, your PDF viewer may not be able to display this type of document.
Care, Tactical, Combat, Casualty, Tactical combat casualty care
White House Liaison and Communications
armypubs.army.milWhite House communications are received by ECC WHLO directly from OSD. ECC WHLO will assign a suspense date ranging from one to 10 working days, depending on the urgency of the request.
Communication, House, White, Liaison, White house, White house liaison and communications
Training Combat Training Center Program - armypubs.army.mil
armypubs.army.milCombat Training Center (CTC) Program. It also designates Headquarters, Department of the Army (HQDA), Deputy Chief of Staff (DCS), G–3/5/7 as the CTC Program Director with program execution authority on behalf of the Chief of Staff,
Information Management Official Mail and Distribution ...
armypubs.army.milInformation Management . Official Mail and Distribution Management Applicability. This memorandum applies to Headquarters, Department of the Army (HQDA) and its field operating agencies. Proponent and exception authority. The proponent of this memorandum is …
Information, Management, Distribution, Officials, Management information, Distribution management, Information management official
Surface Transportation Distribution of Materiel and ...
armypubs.army.milContents—Continued Distribution of materiel goals † 2–3, page 9 Distribution of materiel and force projection † 2–4, page 9 Distribution of materiel system and the Defense Logistics and Global Supply Chain Management System † 2–5,
Surfaces, Management, Distribution, Transportation, Materiel, Surface transportation distribution of materiel
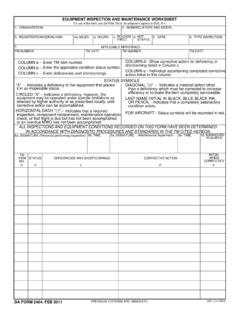
EQUIPMENT INSPECTION AND MAINTENANCE WORKSHEET
armypubs.army.milEnter deficiencies and shortcomings. COLUMN d. shortcoming listed in Column c. Show corrective action for deficiency or. STATUS SYMBOLS COLUMN e. action initial in this column. Individual ascertaining completed corrective "X" Indicates a deficiency in the equipment that places.
Clothing and Individual Equipment - United States Army
armypubs.army.milDA Form 3645, DA Form 3645-1, DA Form 4886 or electronic version as prescribed by AR 710-2. Guidance on transfer of organizational issue items is contained in Appendix F. 5.
United, States, Individuals, Army, United states army, Equipment, Clothing, 6345, Clothing and individual equipment
Additional Organizational and Individual Equipment Record
armypubs.army.milDA FORM 3645-1, DEC 1983. Edition of Jan 82 may be used until exhausted. APD LC v1.00. NAME (Last, First, MI) AND SOCIAL SECURITY NUMBER. INSTRUCTIONS: Overprinting is authorized. Entries in ink (MOS - pencil, Auth of each item possessed by individual. Advance. ALL. totals to next column on .
U.S. Army Continuity of Operations Program Policy and …
armypubs.army.milOperations Program Policy and Planning Headquarters Department of the Army Washington, DC 18 April 2008 UNCLASSIFIED. SUMMARY of CHANGE AR 500–3 U.S. Army Continuity of Operations Program Policy and Planning This rapid action revision, dated 18 April 2008-- ... Requirements for the Army Continuity of Operations Program 5. s.
Programs, Policy, Operations, Planning, Continuity, Continuity of operations, Continuity of operations program policy and, Operations program policy and planning, Continuity of operations program policy and planning
Related documents
National Security Agency | Mobile Device Best Practices
media.defense.govJul 28, 2020 · Update the device software and applications as soon as possible. Consider using Biometrics (e.g., fingerprint, face) authentication for convenience to protect data of minimal sensitivity. Use strong lock-screen pins/passwords: a 6-digit PIN is sufficient if the device wipes itself after 10 incorrect password attempts. Set the device
NIST Cybersecurity Framework Policy Template Guide
www.cisecurity.org802.11 Wireless Network Security Standard Mobile Device Security System and Information Integrity Policy Protect: Awareness and Training (PR.AT) PR.AT-1 All users are informed and trained. Acceptable Use of Information Technology Resources Policy Information Security Policy Personnel Security Policy Physical and Environmental Protection Policy
The Chinese Wall Security Policy - Purdue University
www.cs.purdue.eduTHE CHINESE WALL SECURITY POLICY Dr. David F.C. Brewer and Dr. Michael J. Nash GAMMA SECURE SYSTEMS LIMITED 9 Glenhurst Close, Backwater, Camberley, Surrey, GUI 7 9BQ, United Kingdom ABSTRACT Everyone who has seen the movie Wall Street wi~l have seen a commercial security policy in action. The recent work of Clark and Wilson and the
More reporting formats .3 Writing effectively
www.fao.orgFood Security Communications Toolkit 144 What should a policy brief do? A policy brief should: Provide enough background for the reader to understand the problem. Convince the reader that the problem must be addressed urgently. Provide information about alternatives (in an objective brief). Provide evidence to support one alternative (in an advocacy brief).
Criminal Justice Information Services (CJIS) Security Policy
www.fbi.govJun 01, 2019 · Security Policy Version 5.8 06/01/2019 CJISD-ITS-DOC-08140-5.8 ... Section 5.13.2 Mobile Device Management (MDM): add exception to the MDM requirement for indirect access, Fall 2018, APB#14, SA#2 ...
Policy, Services, Information, Devices, Security, Criminal, Justice, Cjis, Criminal justice information services, Security policy
Mobile Device Acceptable Use Policy
www.wcccd.edu6. IT will manage security policies, network, application, and data access centrally using whatever technology solutions it deems suitable. Any attempt to contravene or bypass said security implementation will be deemed an intrusion attempt and will be dealt with in accordance with WCCCD’s overarching security policy. 7.
Policy, Devices, Security, Mobile, Acceptable, Security policy, Mobile device acceptable use policy