Control Mechanisms
Found 9 free book(s)Assessment of access control systems - NIST
nvlpubs.nist.govcontrol policies, models, and mechanisms to assist them in securing their computer applications. The document discusses the capabilities, limitations, and qualities of the access control mechanisms that are embedded for each access control policy. 1.3 Audience and Assumptions
CATALOG OF DOCTRINE TOPICS - AF
www.doctrine.af.mildefined command relationships and appropriate command and control mechanisms. C2 and organization are inextricably linked. Forces should be organized around the principle of unity of command. Clear lines of authority, with clearly identified commanders at appropriate echelons, exercising appropriate control, are essential to
Chapter 4. Basic Failure Modes and Mechanisms - NASA
parts.jpl.nasa.govMechanisms Possible Solutions Degradation in IDSS Life test, operation Gate sinking, surface effects, hydrogen effects Derating criteria, temperature control, environmental control Degradation in gate leakage current Life test, high-temperature storage test, high-temperature reverse bias Interdiffusion Temperature control, gate current control ...
BASIC MECHANISMS OF CORROSION AND CORROSION …
www.ohiowea.orgMechanisms are identical Corrosion Control for Exterior is Identical Materials, Design and Construction Practices Similar….. But Wastewater construction does not typically account for the eventual need for cathodic protection o Electrical Continuity of Pipelines and Structures o …
Surveillance Report - Centers for Disease Control and ...
www.cdc.govCenters for Disease Control and Prevention, U.S. Department of Health and Human Services. ... Unintentional falls and motor vehicle crashes were the most common mechanisms of injury Rates of TBI-related hospitalizations per 100,000 population were …
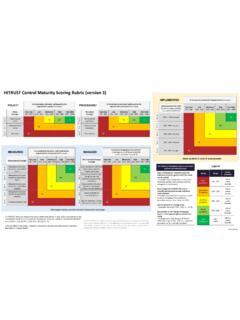
HITRUST Control Maturity Scoring Rubric (version 3)
hitrustalliance.netmechanisms to modify risk. Risk treatment options can include avoiding, optimizing, transferring, or retaining [accepting] risk. [ENISA Glossary of Terms] To be classified as a risk treatment process for HITRUST assessment purposes,the process must include: (i) initial involvement of an appropriate level of management or a defined escalation or ...
Design Principles - Clemson
www.cs.clemson.eduSecurity mechanisms should be as simple as possible. This principle simplifies the design and implementation of security mechanisms. If the design and implementation are simple, fewer possibilities exist for errors. The checking and testing process is less complex. Interfaces between security modules are suspect area and should
Access Control Matrix - Columbia University
www.cs.columbia.eduAccess Control Matrix • List all proceses and files in a matrix • Each row is a process (“subject”) • Each column is a file (“object”) • Each matrix entry is the access rights that subject has for that object Steven M. Bellovin September 12, 2005 1
A COUNTERFACTUAL APPROACH FOR IMPACT EVALUATION
scholar.harvard.eduThe Outcomes for the treated and control individuals are: Yi(1) = Yi(T = 1) for some treatment variable T (Treated). MIGUEL ANGEL LUQUE-FERNANDEZ A COUNTERFACTUAL APPROACH FOR IMPACT EVALUATION. INTRODUCTION COUNTERFACTUAL FRAMEWORK IE DESIGNS & METHODS CASE STUDIES