Extortion With Protection Understanding The
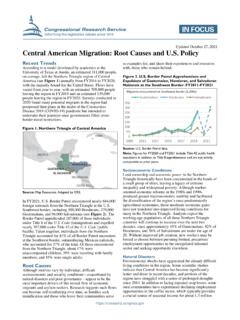
Found 7 free book(s)Central American Migration: Root Causes and U.S. Policy
sgp.fas.orgOct 27, 2021 · extortion, and other illicit activities. The region also ... migration and protection pathways in the United States and third countries. In accordance with the strategy, the ... Information in a CRS Report should not be relied upon for purposes other than public understanding of information that has
Fortinet Partner Code of Conduct
www.fortinet.comany and all forms of bribery, corruption, extortion, kickbacks and embezzlements. Anti- bribery laws, such as the U.S. FCPA, the United Kingdom ... understanding, and complying with the company’s Anti-Corruption Policy. C) Antitrust and Competition Laws: Fortinet is committed to observing rigorously the ... Victims Protection Act and the UK ...
DEPARTMENT OF DEFENSE (DoD) INITIAL TRAINING GUIDE
www.lockheedmartin.comalong with scenario-based exercises that will test your understanding of the material. You will also get to know Security Professionals who can assist and ... situations that could lead to blackmail or extortion • Attempts by foreign customers to gain access ... • Period of time protection is required
Juvenile Delinquency - SAGE Publications Inc
www.sagepub.comfew was passed for the protection of young people and to reduce the incidence of delinquency. ... 62 UNDERSTANDING JUVENILE JUSTICE PROCESS AND SYSTEMS 03-Martin (juvenile).qxd 1/19/2005 2:48 PM Page 62 ... violence, intimidation, and extortion. CHAPTER PERSPECTIVE 3.1 03-Martin (juvenile).qxd 1/19/2005 2:48 PM Page 64.
Addressing Violence against Sex Workers
www.who.intUnderstanding them is key to designing appropriate programmatic responses. ... Sex workers may face violence from extortion groups, militias, religious extremists or “rescue” groups. ... • Promote the full protection of sex workers’ human rights. This includes the rights to: non-
SD-Access Segmentation Design Guide - Cisco
www.cisco.comProtection, and Cisco Stealthwatch® providing network visibility, and Cisco Identity Services Engine providing policy and secured network access for authorized users, guests, and IoT devices are all effective in providing a “defense-in-depth” strategy to protect an organization. Once adopted, the focus shifts to defining an
Matter of A-R-C-G- et al., Respondents
www.justice.govAug 26, 2014 · Cite as 26 I&N Dec. 388 (BIA 2014) Interim Decision #3811 388 Matter of A-R-C-G- et al., Respondents Decided August 26, 2014