Identity And Access
Found 11 free book(s)AHS Identity & Access Management (AHS IAM) Alberta …
www.albertahealthservices.caAHS Identity & Access Management (AHS IAM) Alberta Vaccine Booking System (AVBS) Licenses / Access Provisioning User Guide . This guide supports both: • AVBS Authorized Approvers managing licenses / access for AVBS endusers in community facilities. - AND
DoD Enterprise Identity, Credential, and Access Management ...
dodcio.defense.govIdentity, Credential, and Access Management (ICAM) Reference Design Version 1.0 June 2020 Prepared by Department of Defense, Office of the Chief Information Officer (DoD CIO) DISTRIBUTION STATEMENT C. Distribution authorized to U.S. Government agencies and their contractors (Administrative or Operational Use).
Cyber Security 101 - CMU
www.cmu.eduJun 20, 2006 · Intrusion – Unauthorized individuals trying to gain access to computer systems in order to steal information . Virus, Worm, Trojan Horse (Malware) – programs that infect your machine ... Report identity theft to your local police department 2. Contact the fraud hotline at the Social Security Administration (SSA), if your social security was ...
Identity and Access Management - Oracle
www.oracle.comIdentity and Access Management • Identity and Access Management (IAM) service enables you to control what type of access a group of users have and to which specific resources • Resource is a cloud object that you create and use in OCI (e.g. compute instances, block
Identity and Access Management Overview
www.cpd.iit.edu11 Identity and Access Management Presentation Current Challenges with I&AM ―64% of respondents say they have deployed an identity and access management system (IAM)‖ ―Almost 60% of respondents say their companies are unable to effectively focus IAM controls on areas of the greatest business risk‖
Identity and Access Management - Institute of Internal …
chapters.theiia.orgIdentity and access management (IAM) is the process of managing who has access to what information over time. This cross-functional activity involves the creation of distinct iden-tities for individuals and systems, as well as the association of system and application-level accounts to these identities.
Chase Identity Theft Protection Kit
www.chase.com• A signed and completed Identity Theft Report or Identity Theft Fraud and Forgery Declaration form. For your convenience, you can: • Complete the Identity Theft Report online at the website of the Federal Trade Commission (FTC) at identitytheft.gov. • Call 1-877-IDTHEFT (1-877-438-4338) to request the FTC Identity Theft Report.
IdentityTheft.gov A Recovery Guide
www.consumer.ftc.govLets you have access to your credit report as long as companies take steps to verify your identity Stops all access to your credit report unless you lift or remove the freeze Free to place and remove if someone stole your identity. Guaranteed by federal law Cost and availability depend on your state law. There might be a small fee for placing ...
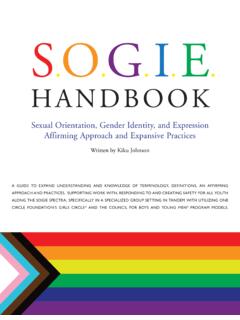
HANDBOOK
www.health.ny.govidentity and/or sexual orientation and are seeking safe spaces and relationships within a supportive community. Adolescence is a time of self-exploration and identity development. Anywhere from 1-15% of youth identify as LGBTI at any given time.7 LGBT youth are more vulnerable to mental health risks including depression, suicide, addictions and
BORN FREE AND EQUAL - OHCHR | Home
www.ohchr.orggender identity or sex characteristics,6 are entitled to enjoy the protections provided by international human rights law, including rights to life, security of person and privacy, the right to be free from torture, arbitrary arrest and
Identity Theft Affidavit - Consumer Information
www.consumer.ftc.govreport identity theft and get a recovery plan. This plan includes the forms, affidavits, and letters you will need as the site helps ...