Role Based Access Control Rbac
Found 6 free book(s)Research Paper: Information Security Technologies
www.secureconsulting.netof security models, including Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC). A standard ACM provides an interface through which a user will self-identify, followed by a mechanism for challenging and confirming that identity, and then a method for granting rights, or access to ...
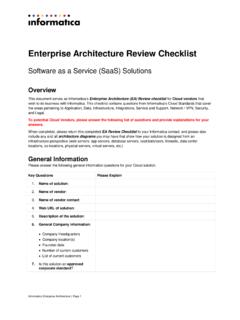
Enterprise Architecture Review Checklist - Informatica
www.informatica.com7. Does the solution provide the ability to control application functionality access by roles for all users, also referred to as Roles Based Access Control (RBAC), via methods such as by attribute or based on a hierarchy? 4. Does the solution provide the ability to audit and export user accounts and historical user activity? 5.
MS120 Switches - Cisco Meraki
meraki.cisco.comRole-based access control (RBAC) with granular device and configuration control Corporate wide password policy enforcement IEEE 802.1X RADIUS and …
KIP Windows Driver Installation & User Guide
kipnews.kip.comUsing Role Based Access Control (RBAC) with the KIP Windows Driver.....39 Appendix 4 ... based application for both Color and B&W print applications. 2-way communication with KIP systems . Displays current media information and real time system status .
Citrix NetScaler Deployment Guide
www.citrix.comRole-based access control (RBAC) Function consolidation Deployment and Management Investment protection. 6 citrix.com White Paper Operational visibility Network Topology Where Does a NetScaler Fit in the Network? NetScaler resides in front of web and applications servers, so that client requests and server
Deploy an endpoint detection and response (EDR) solution ...
raw.githubusercontent.comwizard in the Microsoft Defender Security Center which includes role-based access control (RBAC), data retention policies, organizational size, geographical storage locations, and the option to use preview features Deploy an endpoint detection and response (EDR) solution with Microsoft Architect Microsoft Defender for Endpoint for your