Search results with tag "Trojan"
The Iliad, The Odyssey, - Kyrene School District
www.kyrene.orgbitter war between the Greeks and Trojans over the capture of the Spartan queen Helen by Trojan prince Paris, is a prequel toThe Odyssey and The Aeneid. The Odysseytells of the Greek warrior Odysseus’s adventurous journey home after the Trojan War. The Aeneid is the story of the refugee Trojan prince Aeneas and his long journey to find a new ...
The Trojan War: Main Characters
tdps.berkeley.eduthe Trojan War Menelaus served under his elder brother Agamemnon, the commander in chief of the Greek forces. After the fall of Troy, Menelaus recovered Helen and brought her home never actually executing her as promised in the play, Trojan Women. Talthybius (Ancient Greek: Ταλθύβιος) was herald and friend to Agamemnon in the Trojan ...
Breaking the Target: An Analysis of Target Data Breach and ...
people.cs.vt.eduTrojan [11]. This Trojan was initially installed through a phishing attempt. Due to the poor security training and security system of the third party, the Trojan gave the attackers full range of power over the company’s system [10]. It is not known if Fazio Mechanical Services was targeted, or if it was part of a larger phishing
The Apple of Discord The Story of the Trojan War
www.wboro.orgGreece Name: Homer, the blind poet, documented the events of the Trojan War back in 800 B.C. in The Iliad, the first of Homer’s two epics relating to the ancient Greeks. The Iliad has been translated into many languages, and is a part of curriculums around the world. It chronicles a battle and is based on the real Trojan War.
6 VOLT - Trojan Battery Company
www.trojanbattery.comTrojan Battery Company reserves the right to make adjustments to this publication at any time, without notice or obligation. 800.423.6569 / +1.562.236.3000 / trojanbattery.com T-105.DS_020819 A. The number of minutes a battery can deliver when discharged at a constant rate at 80°F (27°C) and maintain a voltage above ...
Thursday, January 20, 2022 Students recount isolation ...
adobeindd.comThursday, January 20, 2022 | STUDENT NEWSPAPER OF THE UNIVERSITY OF SOUTHERN CALIFORNIA SINCE 1912 | VOL. 205, NO. 3 daILy TrOJan INDE 1 · News 3 · Opinion 4 · A & E 6 · Classifieds 5 · Sudoku 8 · Sports DAILYTROJAN.COM DAILYTROJAN By ChrIsTIna ChKarBOuL News Editor When Catherine Chen found out she’d have to isolate after test-
Euripides Trojan Women - The Kosmos Society
kosmossociety.chs.harvard.eduEuripides Trojan Women Translated by E. P. Coleridge. Revised by the Trojan Women Heroization team (Hélène Emeriaud, Kelly Lambert, Janet M. Ozsolak, Sarah Scott, Keith Stone) Before Agamemnon’s tent in the camp near Troy.
The Argus-Press Thurs., Oct. 17, 2013 TROJAN TIMES
images.pcmac.orgTROJAN TIMES OOwosso Public Schools † www.owosso.k12.mi.us † Ready for the World!wosso Public Schools † www.owosso.k12.mi.us † Ready for the World! ... Our Equestrian Team won the Michigan Interscholastic Horse-manship Association State Championship this past weekend. Team ... gan Interscholastic Horsemanship Association Division C ...
T H E I L L U S T R AT E D ODYSSEY - Mythweb
www.mythweb.comThe Trojan War was over. The clever Greek Odysseus had tricked the enemy into bringing a colossal wooden horse within the walls of Troy. The Trojans had no idea that Greek soldiers were hidden inside, under the command of Odysseus. The Greeks had been been laying siege to Troy for nine long years, but suddenly it looked like their whole
Greek mythology - MS. TIMMEL'S CLASSES
timmel.weebly.comthat caused the Trojan War, but if you ask her she would tell you it was her half-sister, Helen’s, fault. In the legend of the Golden Apple of Discord Hera, Athena, and Aphrodite all claimed to be the fairest goddess. Paris, the Prince of Troy, awarded it to Aphrodite beginning a chain of events that led to the Trojan War.
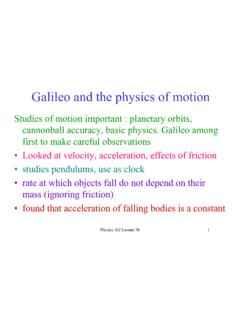
Galileo and the physics of motion
www.nicadd.niu.eduTrojan points of Jupiter One asteroid found at Earth’s Trojan point. See 162 webpage . Physics 162 Lecture 3b 17 Kepler’s Laws • Kepler’s Laws can all be derived from Newton’s laws of motion and force of gravity • gravity causes elliptical orbits where planet moves faster when closer to the Sun as force of gravity is larger there ...
F TROJAN BATTERY COMPANY 1 LEAD / ACID BATTERY H 2 R
www.trojanbattery.comhazard rating trojan battery company lead / acid battery material safety data sheet section 1-- chemical product and company identification manufacturer's
British-World Literature Reading List
www.windham-schools.orgWar and Peace Turgenev, Ivan Fathers and Sons Greek/Roman Aeschylus The Oresteia Aristotle Ethics, Politics Dante The Divine Comedy The Inferno Euripides Alcestis Medea Hipploytus Trojan Woman Electra Bacchae Herodotus The Histories Homer The Illiad The Odyssey Lucretius On the Nature of Things Marcus Aurelius The Meditations Plato Great ...
THE ILIAD OF HOMER - University of Chicago Press
press.uchicago.eduhistory oftheir own race was the Trojan War. As to the details ofthis war, as to the interpretation ofits causes and its meaning, there might be disagreement; but for most persons at least, it was a piece ofhistory, not a piece oflegend ormyth; and the main characters and the essential course ofevents were matters ofgeneral agreement.
Tales from Ancient Greece - BBC
downloads.bbc.co.ukSchool Radio www.bbc.co.uk/schoolradio © BBC 2013 School Radio Tales from Ancient Greece 1 6. ODYSSEUS AND THE TROJAN HORSE HERMES The young men of …
Marine and RV - Trojan Battery Company
www.trojanbattery.comMarine and RV Made in USA Aerial Work Platform / Access Floor Cleaning Golf / Utility Vehicle / NEV Material Handing Marine / RV Transportation Renewable Energy / Backup
DATA SHEET - Trojan Battery
www.trojanbattery.comDATA SHEET Designed in compliance with applicable BCI, DIN, BS and IEC standards. Tested in compliance to BCI and IEC standards. OPERATIOAL DATA
DEEP-CYCLE GEL BATTERIES - First National Battery
www.battery.co.zaPage 1 of 2 PRODUCT LINE SHEET for Renewable Energy and Backup Power Applications DEEP-CYCLE GEL BATTERIES BATTERY: VRLA GEL DIMENSIONS: inches (mm) COLOR: Maroon (case) Grey (cover) MATERIAL: Polypropylene Trojan’s deep-cycle gel batteries are sealed, maintenance-free batteries that deliver superior power in demanding renewable
8D-AGM DATA SHEET - Trojan Battery Company
www.trojanbattery.comDaily Charge 14.1 – 14.7 28.2 – 29.4 42.3 – 44.1 56.4 – 58.8 Float 13.5 27 40.5 54 Do not install or charge batteries in a sealed or non-ventilated compartment.
24AGM DATA SHEET - Trojan Battery
www.trojanbattery.com24-AGM DATA SHEET For a Troan Master Distriutor near you, call 8.423.656 or 1.562.236.3 or isit ww.troanattery.com 12380 Clark Street, Santa Fe Springs, CA 90670 • USA
DATA SHEET T- - Trojan Battery Company
www.trojanbattery.comDATA SHEET T- OPERATIONAL DATA Opera Temperature S ischarge-4F to 113F (-20C to +45C). At temperatres below 32F (0C) maintain a state o charge greater than 60.
Greek Allusions in Everyday Life - Chino Valley Unified ...
www.chino.k12.ca.usMars was the Greek God of war. The Mars Bar battles against hunger. Surprisingly, this is not a true allusion. The candy bar got it name from the company owner Forrest Mars, not the ... The Trojan Horse and Greek Columns greet visitors at the main entrance. PHOENIX, ARIZONA The largest capital city in the USA, Phoenix, Arizona, got its name ...
RODZINA XXI WIEKU - Aktualności
e-pedagogiczna.edu.pl1 RODZINA XXI WIEKU Zestawienie bibliograficzne w wyborze Opracowanie: Elżbieta Trojan. Pedagogiczna Biblioteka Wojewódzka w Opolu Niniejsze zestawienie bibliograficzne poświęcone zostało problemom współczesnej rodziny przełomu
Nursing and Caring: An Historical Overview from Ancient ...
www.internationaljournalofcaringsciences.orgwounded during the Trojan War (Morford et al., 2011). Ancient Greeks worshiped Apollo the Sun God as the God of healing, while Asclepius, the son of Apollo, was the Greek God of medicine. Apollo’s daughter Hygiea was the goddess of health and was credited for magical cures. In that era, much emphasis was given to personal
Web Shells, Backdoor Trojans and RATs - Akamai
www.akamai.comWeb shells are installed on a Web server through a compromise of some kind. The compromise could be through a legitimate Web application on the server using techniques like SQL injection, Remote File Inclusion, an unvalidated file upload feature or through a
The Essential Odyssey - i am awesome
mrleeisawesome.weebly.comIt was a central theme of the Trojan legend that getting home again was at least as great a challenge for the Greeks as winning the war. Many heroes lost their homecomings by dying at Troy, including Achilles, the greatest warrior of the Greeks, whose decision to fight in the full knowledge that he would
Next Generation Guardmaster Safety Relay (GSR) Wiring …
literature.rockwellautomation.com24 CI Trojan T15, Elf, E-stop, PLC on Ch2 100S-C 2 3 d 0 26 CI (3) SensaGuard 100S-C 3 4 e 0 ... Faults are only detected at these times because any switching between the first opening and last closing does not change the state of the monitoring unit input circuits.
AC Greece FINAL copy - Aurora Public Schools
aurorak12.orgThe Trojan War occurred during this period. The age of the city-states was between 1100 to 700 BC. Only a few cities had kings, and others were moving towards democracy, where each person had a vote in matters of state. The wealth of the Greeks grew as they traded more widely in the ...
Common Cyber Threats: Indicators and Countermeasures
securityawareness.usalearning.govIt puts your personal information and your organization’s information at risk. Spear phishing is a type of targeted phishing that appears to be directed towards a ... • Trojan horses • Worms • Keyloggers • Spyware • Rootkits • Backdoors . Indicators .
History of the Kings of Britain - York University
www.yorku.caAfter the Trojan war, Aeneas, flying with Ascanius from the destruction of their city, sailed to Italy. There he was honourably received by king Latinus, which raised against him the envy of Turnus, king of the Rutuli, who thereupon made war against him. Upon their engaging in battle, Aeneas got the victory, and having killed Turnus,
CompTIA Security+ Certification Exam Objectives
comptia.jp- Remote access Trojan (RAT) - Rootkit - Backdoor • Password attacks - Spraying - Dictionary - Brute force - Offline - Online - Rainbow table - Plaintext/unencrypted • Physical attacks - Malicious Universal Serial Bus (USB) cable - Malicious flash drive - Card cloning - Skimming • Adversarial artificial intelligence (AI) - Tainted ...
Supplier Access Terms 10 April 2020 - Jaggaer
www.jaggaer.comWe reserve the right at all times to disclose information as we deem necessary to defend our legal rights, satisfy applicable law or respond to a ... that contains a virus, bug, cancelbot, worm, Trojan Horse or other harmful item; (iv) publish, perform, distribute, prepare derivative works, copy, or reverse engineer (except
Topic 7.2 INTRODUCTION TO DRUG DESIGN
www.chem.uwec.edu• Quick recovery times after surgery 1.2.9 Introducing chemically susceptible groups N CH 2 C O O MeO OMe H MeO (CH)5O C OMe O CH Me MeO OMe OMe OMe 1.2 Drug stability. ... Trojan horse tactic 1.3.1 Linking a biosynthetic building block 1.3 Drug targeting Non selective alkylating agent Toxic N Cl Cl H 3C Uracil Mustard H N HN O O N Cl Cl.
Threats and Attacks
web.cse.ohio-state.eduTrojan horses, and active Web scripts aiming to steal or destroy info. •Backdoor: accessing system or network using known or previously unknown mechanism •Password crack: attempting to reverse calculate a password •Brute force: trying every possible combination of options of a password •Dictionary: selects specific accounts to attack
The History of the Peloponnesian War By Thucydides
people.duke.educonviction of the weakness of ancient times. Before the Trojan war there is no indication of any common action in Hellas, nor indeed of the universal prevalence of the name; on the contrary, before the time of Hellen, son of Deucalion, no such appellation existed, but …
CU250S-2 Control Units - Siemens
cache.industry.siemens.comSoftware manipulation (e.g. by viruses, Trojan horses, malware, worms) can cause unsafe operating states to develop in your installation which can result in death, severe injuries and/or material damage. • Keep the software up to date. You will find relevant information and newsletters at this address
ASEAN CYBERTHREAT ASSESSMENT 2021
www.interpol.intIn addition to cyberthreats such as ransomware, phishing and Remote Access Trojan malware, different types of cyber frauds are highlighted in this report as the latter, in particular, presents a persistent problem to the ASEAN region. Indeed, as soon as it was captured on our radar, the ASEAN Desk was able to lead on-the-ground action
Incident Reporting - United States Army
armypubs.army.milMalicious logic infection (for example, virus, worm, trojan). (g) Receipt of suspicious e-mail attachments, files, or links. 2 . DA PAM 25–2–17 • 8 April 2019 (h) Violations of cybersecurity policy and mandatory procedures in AR 25 ...
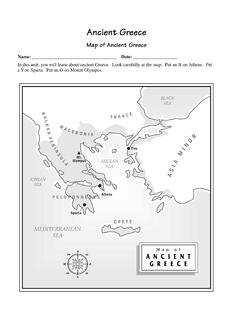
Ancient Greece - 6th Grade Social Studies
nsms6thgradesocialstudies.weebly.comTrojan War—legendary battle between the ancient Greeks and the people of Troy in the 12th or 13th century B.C. Early Greek Civilizations Brief #1 The physical geography of any place is an important key in understanding how and why its civilization developed the way it did.
Chapter 1 Introduction to Ethical Hacking
media.techtarget.comMalicious software (malware) includes viruses, worms, Trojan horses, and spyware. Malware clogs networks and takes down systems. Spam (junk e-mail) is wreaking havoc on system availability and storage space. And it can carry malware. Ethical hacking helps reveal such attacks against your computer systems.
THE JEWS DECLARE WAR ON GERMANY (1933).
newamericangovernment.org"The war now proposed is for the purpose of establishing Jewish hegemony throughout the . world." - Brigadier General George Van Horn Mosely, The New York Tribune, March 29, 1939. ... within the resistance. And we are the Trojan horses in the enemy's fortress. Thousands of Jews living in Europe constitute the principal factor in the destruction ...
Trojan Source: Invisible Vulnerabilities
trojansource.codescall Trojan-Source attacks, and which use maliciously encoded but semantically permissible source code modi-fications to introduce invisible software vulnerabilities. We provide working examples of Trojan-Source vulner-abilities in C, C++, C#, JavaScript, Java, Rust, Go, and Python. We describe effective defenses that must be employed by
TROJAN BATTERY COMPANY LEAD ACID BATTERY WET, …
www.trojanbattery.compage 1 of 10 hazard rating trojan battery company . lead acid battery wet, filled with acid safety data sheet. section 1 — product and company identification
TROJAN 2 7 0 - Angus Air
www.angus-air.co.ukTROJAN 2 7 0 Chassis panelwork is all ‘In House’ manufactured from nominally 1.2mm Galvanised steel. Where at all possible, flanges are formed inward facing to prevent exposure to bare metal edges. Sufficient forms and folds are incorporated to provide a vibration free, robust structure.
Similar queries
Kyrene School District, Trojan, Trojan War, The Trojan War, Agamemnon, Breaking the Target: An Analysis, The Trojan, Euripides Trojan Women, TROJAN TIMES, Michigan Interscholastic Horse-manship Association, Interscholastic Horsemanship Association, Odyssey, Greek mythology, TROJAN BATTERY COMPANY, LEAD / ACID, Trojan battery company lead / acid, Literature Reading List, Tales from Ancient Greece, THE TROJAN HORSE, Marine and RV, DATA SHEET, Trojan Battery, DATA, Deep-cycle gel batteries, 8D-AGM DATA SHEET, Batteries, 24AGM DATA SHEET, 24-AGM DATA SHEET, DATA SHEET T- - Trojan Battery Company, DATA SHEET T, Web Shells, Backdoor Trojans and RATs, Shells, Safety Relay, Times, Aurora Public Schools, Your, Supplier Access Terms, Reporting, United States Army, Ancient Greece, Chapter 1 Introduction to Ethical Hacking, THE JEWS DECLARE WAR ON GERMANY 1933, TROJAN BATTERY COMPANY LEAD ACID BATTERY, Trojan battery company . lead acid battery, TROJAN 2 7 0