Search results with tag "Se curity"
Human Security - Human Development Reports
hdr.undp.orgHuman security relates to much more than secu-rity from violence and crime. A report team wanting to look at the security of people’s livelihoods (eco-nomic, food, environment or health security) might apply a human security approach. Human security can also be used to look into personal, community and political security. Indeed, human ...
Withdrawn NIST Technical Series Publication
nvlpubs.nist.govaddresses security from both a functionality perspective (the strength of secur ity functions and mechanisms provided) and an assurance perspective (the measures of confidence in the implemented security capability). Addressing both security functionality and security assurance
What Is National Security? - The Heritage Foundation
www.heritage.orga National Security Strategy. ... Peace and stability could be better served if people were not slaughter- ... security; and even health, women’s, and food secu-rity. This proliferation of ...
Digital Identity Guidelines - NIST
nvlpubs.nist.govthe cost -effective security and privacy of other than national s ecurity-related information in f ederal information systems. The Special Publication 800 -series reports on ITL’s research, guidelin es, and outreach efforts in information system security, and its collaborative activities with industry, government, and academic organizations.
CHAPTER User Management and Security in SAP Environments
cdn.ttgtmedia.comSAP/R3 Handbook 3e / Hernandez / 0072257164 / CH8 8 User Management and Security in SAP Environments S ecurity is increasingly being considered one of the key points to boost electronic
DoD 7000.14 - R DEPARTMENT OF DEFENSE FINANCIAL …
comptroller.defense.govcrime operations, maritime and border security operations, military intelligence operations, and operations or activities that contribute to an international coalition operation that is determined by the Secretary to be in the national interest of the United States per . 10 U.S.C. § 333, Foreign s ecurity forces: authority to build capacity ...
Minimum Standards in Food Security and nutrition
www.spherehandbook.orgMinimum S tandards in ood f S ecurity and utritionn 143 Introduction Links to the Humanitarian Charter and international law The minimum standards for food security and nutrition are a practical expres-
Nighthawk X6 AC2200 Tri-Band WiFi Range Extender
www.downloads.netgear.comWPS does not support WEP network security or a hidden SSID network. If your existing WiFi netw ork uses WEP secur ity or its SSID is hidden, f ollow the instr uctions in Connect With the NETGEAR Installation Assistant on page 14. Note Get Started 12 Nighthawk X6 AC2200 Tri-Band WiFi Range Extender.
An Introduction to Privacy Engineering and Risk …
nvlpubs.nist.govthe cost -effective security and privacy of other than national s ecurity-related information in f ederal systems. Abstract . This document provides an introduction to the concepts of privacy engineering and risk management for federal systems. These concepts establish the basis for a common vocabulary to
BASIC AIX S ECURITY - Circle4.com
www.circle4.com10/16/2013 4 UNIX S ECURITY BASICS Permissions UID GID Dangerous Accounts Superuser SUID Sticky bit Umask Backups 7 PERMISSIONS r read w write x execute s SUID or SGID t sticky bit e Encrypted
S/RES/827 (1993) RESOLUTION 827 (1993)
www.icty.orgUNITED NATIONS -----~-----Secu rity Cou nei I RESOLUTION 827 (1993) Distr. GENERAL S/RES/827 (1993) 25 May 1993 Adopted by the Security Council …
HP LaserJet MFP M438 series
h20195.www2.hp.comData sheet HP LaserJet MFP M438 series Count on legendar y HP per formance and reliabilit y at an af fordable price. Sur pass your of fice printer expectations with the speed, qualit y, and ef ficienc y of HP LaserJet of fice printers. HP LaserJet MFP M438n HP LaserJet MFP M438dn HP LaserJet MFP M438nda Dynamic securit y enabled printer.
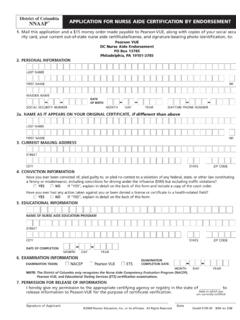
NNAAP APPLICATION FOR NURSE AIDE CERTIFICATION BY …
doh.dc.govMail this application and a $15 money order made payable to PearsonVUE, along with copies of your social secu rity card, your current out-of-state nurse aide certificate/license, and signature-bearing photo identification, to: Pearson VUE DC Nurse Aide Endorsement PO Box 13785 Philadelphia, PA 19101-3785 2. PERSONAL INFORMATION
Tackling Terrorists’ Exploitation of Youth
www.un.orgterrorist groups can still present a significant secu-rity threat. During the Second Chechen War in the early 2000s, more than two-thirds of suicide bomb-
Army Cross Domain Solution and Data Transfer Management
armypubs.army.milApr 12, 2019 · approach to addressing the shared -risk associated with the connection of networks of different secu rity domains. The step - by-step connection approval process for SABI CDS is documented in the DISN CPG 5.1 Appendix H.
Similar queries
Human security, Human, Secu-rity, Security, Human security approach, Secur ity, The Heritage Foundation, Security Strategy, Peace, Women, Digital Identity Guidelines, S ECURITY, CHAPTER User Management and Security in SAP, User Management and Security in SAP, Interest, Minimum Standards in Food Security and nutrition, Food security and nutrition, NETGEAR, An Introduction to Privacy Engineering and Risk, An introduction, Privacy engineering and risk management, BASIC AIX S ECURITY, RESOLUTION 827, UNITED NATIONS, Secu rity, Distr, GENERAL S, Security Council, HP LaserJet MFP M438 series, Data, Securit y, Cross Domain Solution