Search results with tag "Hashing"
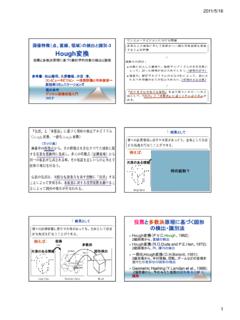
画像特徴(点、直線、領域)の検出と識別-3 Hough変換
web.wakayama-u.ac.jpBasis Geometric Hashing Wolfson and Rigoutsos, Geometric Hashing, an Overview, 1997 全ての2点の組合せから 生成される基底に対して それぞれ不変特徴を求め、 それらを全てHash Table に 登録しておく Wolfson and Rigoutsos, Geometric Hashing, an Overview, 1997 Basis Geometric Hashing 4 1 3
One-sided RDMA-Conscious Extendible Hashing for ...
www.usenix.orgRACE hashing leverages a lock-free remote concurrency con-trol scheme to enable different clients to concurrently operate the same hashing index in the memory pool in a lock-free manner. To resize the hash table with low overheads, RACE hashing leverages an extendible remote resizing scheme to reduce extra RDMA accesses caused by extendible ...
Question Bank - Jeppiaar Engineering College
jeppiaarcollege.orgHashing-Hash functions-Separate chaining-Open Addressing-Rehashing- Extendible hashing. C ou r s e O u t c om e s (C O s ) ... Tables C203.1 BTL 1 4 How data structures are classified? Data structures are classified into two categories based on how the data items are
-33 Hough 変換
web.wakayama-u.ac.jpBasis Geometric HashingBasis Geometric Hashing 拡大 縮小 回転 平行移動 点4と点1から生成された基底に基づいて、 Hash Tableにモデルを登録するイメージ Wolfson and Rigoutsos, Geometric Hashing, an Overview, 1997 Hash Tableにモデルを登録するイメージ
Introduction to Hash Tables
www.sas.comThink FAST! Use Memory Tables (Hashing) for Faster Merging. SUGI 31 Paper 244-31 Gregg P. Snell, Data Savant Consulting, Shawnee, KS Find() the power of Hash - How, Why and When to use the SAS® Hash Object. John Blackwell, NESUG 2010. SAS Hash Object Programming Made Easy. Michele M. Burlew. SAS Press 2012. Better Hashing in SAS 9.2.
7010T Gigabit Ethernet Data Center Switches
www.arista.comthrough an in-memory database. This multi-process state sharing architecture ... •Flexible hash algorithms for efficient hashing, persistent hashing and custom lookups for tunneled protocols * ... Cloud network scalability is directly impacted by the size of a switches forwarding tables. In many systems discrete fixed sized tables are
7060X and 7260X Series 10/25/40/50/100G Data Center …
www.arista.comEOS processes run in their own protected memory space and exchange state through an in-memory database. ... •Custom hash algorithms for efficient hashing, persistent hashing and custom lookups for tunneled protocols. ... adopted using discrete fixed size tables for each of the common types of forwarding entry.
244-31: Think FAST! Use Memory Tables (Hashing) for …
www2.sas.com1 Paper 244-31 Think FAST! Use Memory Tables (Hashing) for Faster Merging Gregg P. Snell, Data Savant Consulting, Shawnee, KS ABSTRACT The objective of this paper is to present a simple way to merge datasets using memory tables.
REMOTE ACCESS VPN NETWORK DIAGRAM
www.network-insider.netObjective 5: Configuring IPSec Policy For Remote Access VPN Client Define the IPSec policy name, encryption type and hashing method. The data
Rapid object indexing and recognition using enhanced ...
link.springer.combetween every feature of every model and every feature of the unknown image. Lamdan and Wolfson [11] first suggested the geometric hashing technique, which was …
Introduction to SAS® Hash Objects
support.sas.comsearching algorithm…" (Dorfman, 2001, p. 1). He demonstrated that in-memory table look-ups (or, direct address searches) could be programmed by hand in order to do the types of in-memory searches performed by the modern hash object. He described three such methods—key-indexed search, array as a bitmap, and hashing—that all have
Chapter 14: Databases and Database Management Systems
www.oakton.edu•Relationships between the tables in the database •Basic information about each table, such as the current ... –Uses hashing algorithms to specify the exact storage location ... •Data is stored in main memory •Dramatically faster than disk-based databases
Course Outcomes(CO)
cse.gndec.ac.inincluding B‐tree, and hashing. c) Learn and apply Structured query language (SQL) for database definition and database manipulation. ... Understand the concepts of different type of geometric transformation of objects in 2D and 3D. e) Understand the practical implementation of modeling, rendering, viewing of objects in 2D.
HyperLogLog: the analysis of a near-optimal cardinality ...
algo.inria.fra geometric mean1. The idea of using harmonic means originally drew its inspiration from an insight- ... As a consequence, using m= 2048, hashing on 32 bits, and short bytes of 5 bit length each: cardinalities till values over N = 109 can be estimated with a typical accuracy of 2% using 1.5kB (kilobyte) of storage.
Fast Probabilistic Collision Checking for Sampling-based ...
gamma.cs.unc.edusearch algorithms, especially the locality-sensitive hashing ap-proaches, which make up our toolbox for accelerating collision queries. A. Collision Checking for Motion Planning One important feature of sampling-based motion planners is the use of exact collision queries to probe the connectivity of C free. However, the topology of C
Data Structures for Databases
www.cise.ufl.edutrees, hashing). Hence, we will focus mainly on their application but also introduce other important data structures to solve some of the fundamental data management problems such as query processing and optimization, e–cient representation of data on disk, as well as the transfer of data from main memory to external storage. However, due to ...
Expectation of geometric distribution Variance and ...
www.cs.cornell.eduHashing Revisited Remember hash functions: We have a set S of n elements indexed by ids in a large set U Want to store information for element s 2 S in loca-tion h(s) in a \small" table (size ˇ n) E.g., U consists of 1010 social security numbers S consists of 30,000 students; Want to use a table of size, say, 40,000.
Hash Tables: Handling Collisions
courses.cs.washington.eduHash Tables: Handling Collisions CSE 373: Data Structures and Algorithms Thanks to Kasey Champion, Ben Jones, Adam Blank, Michael Lee, Evan McCarty, Robbie Weber, Whitaker ... -Everything is stored as bits in memory and can be represented as an integer. ... Double hashing Strategies to handle hash collision
Optimising the SHA256 Hashing Algorithm for …
nicolascourtois.comAbstract Since its inception in early 2009, Bitcoin has attracted a substantial amount of users and the popularity of this decentralised virtual …
Hashing & Hash TablesHashing & Hash Tables
eecs.wsu.eduit d ti the hashtable 18 integers and string keys Cpt S 223. School of EECS, WSU. Implementation of Chaining Hash Table This is the hashtable’s current capacitycurrent capacity (aka. “table size”) This is the hash table ... Disadvantages