Government Transformation Strategy
• the Government Transformation Strategy; • additional detail covering background, scope, specific objectives, government beyond 2020 and the role of the Government Digital Service (GDS); and • appendices, including case studies, services and data registers that have been and will be delivered. This document sets out the strategy in full.
Tags:
Data, Transformation, Strategy, Transformation strategy
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
The quality of clinical coding in the NHS
assets.publishing.service.gov.ukFor the past seven years the Payment by Results data assurance framework has provided assurance over the quality of the data that underpin payments in the NHS.
UNITED KINGDOM ANTI-CORRUPTION STRATEGY …
assets.publishing.service.gov.ukfinancial centre 35 3.3 romote integrity across the public and private sectors P 42 3.4 educe corruption in public procurement and grants R 48
ESF Guidance on Document Retention
assets.publishing.service.gov.uk1 england european social fund operational programme 2014-20 guidance on document retention, including electronic data exchange, for 2014-20 esf projects
Social Security and Child Support SSCS1
assets.publishing.service.gov.ukPage 1 Social Security and Child Support Notice of appeal against a decision of the Department for Work and Pensions You should use this form to appeal against a decision made by the Department for Work and Pensions (DWP) about social
Atingsa, Appeal, Decision, Made, Appeal against a decision, Appeal against a decision made
The Midlands Engine for Growth - …
assets.publishing.service.gov.ukThe Midlands Engine for Growth This prospectus brings the Midlands Engine for Growthto life. It signals willingness from all regional stakeholders to
Growth, Engine, The midlands engine for growth, Midlands, The midlands engine
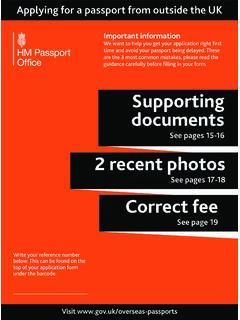
Applying for a passport from outside the UK
assets.publishing.service.gov.uk1 Things you need to know Get it right • This guidance is for British applicants from certain countries applying for a passport from outside the UK, using the OS application …
Outdoor advertisements and signs: a guide for …
assets.publishing.service.gov.ukOutdoor advertisements and signs:a guide for advertisers Advertisement control This booklet, prepared by Communities and Local Government, aims to explain to everyone who wants to display an outdoor advertisement how
Department of Health Review: Final Report
assets.publishing.service.gov.ukMental Health, Disability and Equality Department of Health Room 313A Richmond House 79 Whitehall SW1A 2NS
The constitution of governing bodies of maintained …
assets.publishing.service.gov.ukThe constitution of governing bodies of maintained schools . Statutory guidance for governing bodies of maintained schools and local authorities in England
Contract Management : The Commercial Role
assets.publishing.service.gov.ukContract Management is a team activity involving project, finance and commercial staff. However, this CPS is created as definitive policy on the role of
Related documents
Reporting Made Easy: 3 Steps to a Stronger KPI Strategy
www.qlik.comKPI overload isn’t the only challenge in building the right KPI strategy. Businesses today are struggling with two other key components. First, there’s confusion about lagging versus leading indicators, and which to use where. And second, even when businesses know how crucial data is to their competitive edge, many aren’t
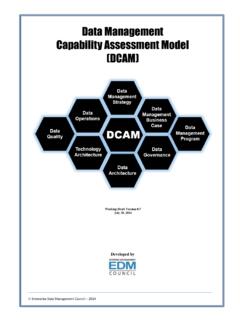
Data Management Capability Assessment Model (DCAM)
dgpo.orgJul 30, 2014 · The DCAM is organized into eight core components. 1. The Data Management Strategy discusses the elements of a sound data strategy, why it is important and how the organization needs to be organized to implement. 2. The Data Management Business Case and Funding Model addresses the creation of the
7 KEY COMPONENTS OF HEALTH CARE DELIVERY SYSTEM …
myersandstauffer.comOct 07, 2018 · processes so that the integrity of the data remains intact and holds providers accountable. Strong contract compliance monitoring is critical to ensure that applicable requirements are properly honored. Ongoing analysis of performance and routine, in-depth reviews of self-reported information safeguard the program. Health Care Reform Healthier ...
Road Safety Strategy - VISION ZERO
saferoaduse.unhcr.orgJan 26, 2018 · the private sector. Collaboration and partnerships will be essential to leverage knowledge, existing initiatives and ultimately benefit from economies of scale. 8 Global Plan for the Decade of Action for Road Safety, 2011–2020. Geneva, World Health Organization, 2011. Pillar 4 Pillar 1 Pillar 2 Pillar 3 International Coordination of Activities
Data Breach Response Checklist - ed
studentprivacy.ed.gov―A data breach response plan is a high-level strategy for implementing the data breach policy. Individual elements of the plan should cover all phases of the incident response, from reporting the breach and the initial response activities to strategies for notification of affected parties, to breach response review and remediation process.
Strategy for Resource Mobilization
www.cbd.intimplementation of the Strategy, all within appropriate timeframes: Goal 1: Improve information base on funding needs, gaps and priorities 1.1. To improve the existing financial information base through enhancing accuracy, consistency and delivery of existing data and improved reporting on funding needs and shortfalls for the
Chapter 111. Texas Essential Knowledge and Skills for ...
tea.texas.govTexas Essential Knowledge and Skills for Mathematics . Subchapter A. Elementary . Statutory Authority: The provisions of this Subchapter A issued under the Texas Education Code, §§7.102(c)(4), 28.002, and 28.0021(a)(1), unless otherwise noted. §111.1. Implementation of Texas Essential Knowledge and Skills for Mathematics, Elementary, Adopted ...
SUMMARY - U.S. Department of Defense
media.defense.govSep 18, 2018 · subsystems, components, or parts to satisfy military requirements (32 CFR Part 236). 3 “Significant cyber incident” refers to an event occurring on or conducted through a computer network that is (or a group of related events that together are) likely to result in demonstrable harm to the national security interests, foreign