GUÍA DE PRUEBAS OWASP
8 Guía de Pruebas de OWASP. La guía de pruebas que está leyendo cubre los procedimientos y herramienta para probar la seguridad de las aplicaciones.
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Cloud Security – An Overview
owasp.orgdata centers Thus, your cloud provider could be working someplace you may never have heard of, such as The Dalles, Oregon, where power is cheap and fiber is plentiful, or just as easily ... "Cloud Computing Security: Raining On The Trendy New Parade," BlackHat USA 2009,
Computing, Security, Cloud, Data, Cloud security, Cloud computing security
Secure Development Lifecycle - OWASP
owasp.orgOWASP Cheat-Sheet Series Manager ... Security Sprint Approach Every Sprint Approach Security Sprint Approach: Dedicated sprint focusing on application security. Stories implemented are security related. Code is reviewed. ... Planning the security testing phase
Development, Sheet, Planning, Lifecycle, Teach, Sprint, Development lifecycle
Shellshock Vulnerability - OWASP
owasp.orgroot@owasp:~#echo “Bash is a Unix shell written for the GNU Project as a free software replacement for the Bourne shell (sh)” root@owasp:~#echo “Often installed as the system's default command-line interface”
Software Assurance Maturity Model (SAMM)
owasp.orgThe Software Assurance Maturity Model (SAMM) is an open framework to help organizations formulate and implement a strategy for software security that is tailored to the specific risks facing the organization. The resources provided by SAMM will aid in: Evaluating an organization’s existing software security practices.
Model, Assurance, Software, Maturity, Software assurance maturity model
Cookie Security - OWASP
owasp.orgNov 30, 2017 · –The security model has many weaknesses –Don’t build your application on false assumptions about cookie security –Application and framework developers should take advantage of new improvements to cookie security –Beware that not all browsers are using the same cookie recipe (yet)
Introduction to the OWASP Top Ten
owasp.orgFeb 09, 2020 · components Budget for ongoing maintenance for all software projects. A10 Insucient Logging & Monitoring Web Server Site A Web Browser sitea.com GET / X Y Site A Site B DOM + JS SIEM. A10 Insucient Logging & Monitoring You can’t react to attacks that you don’t know about. Logs are important for: Detecting incidents Understanding what happened
Secure Coding Practices - Quick Reference Guide
owasp.orgVersion 2.0 4 Software Security and Risk Principles Overview Building secure software requires a basic understanding of security principles. While a comprehensive review of security principles is beyond the scope of this guide, a quick overview is provided.
NOSQL INJECTION - OWASP
owasp.org4 . 2 SCOPE - DATABASES Database Type Ranking Document store 5. Key-value store 9. Key-value cache 23. Document store 26.
Attacking and Securing JWT - OWASP
owasp.orgJWT Secret Brute Forcing RFC 7518 (JSON Web Algorithms) states that "A key of the same size as the hash output (for instance, 256 bits for "HS256") or larger MUST be used with this
OWASP Application Security Verification Standard 4.0-en
owasp.orgOWASP Application Security Verification Standard 4.0 7 Frontispiece About the Standard The Application Security Verification Standard is a list of application security requirements or tests that can be used by architects, developers, testers, security professionals, tool vendors, and consumers to define, build, test and verify secure applications.
Related documents
VER.3.9 - line.worksmobile.com
line.worksmobile.comリクエストフォージェリ(csrf)等の脆弱性、認証・セッション管理の脆弱性に対する様々なテスト、さら に専用のセキュリティ診断ツールを用いた自動診断と、チェックリストを用いた手動診断を並行して実施
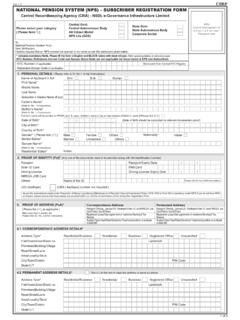
Ver 1.5 NATIONAL PENSION SYSTEM (NPS) – SUBSCRIBER ...
www.npscra.nsdl.co.inVer 1.5 CSRF 1 of 5 Affix recent photograph of 3.5 cm × 2.5 cm size / Passport size NATIONAL PENSION SYSTEM (NPS) – SUBSCRIBER REGISTRATION FORM Central Recordkeeping Agency (CRA) - NSDL e-Governance Infrastructure Limited
Form, System, Registration, Pension, Subscriber, Fcsr, Subscriber registration form, Pension system
Real World Threat Modeling Using the PASTA Methodology
owasp.orgAsset Asset. An asset is a resource of value. It varies by perspective. To your business, an asset might be the availability of information, or