Tips and Tactics: Ransomware - NIST
This infographic is a step-by-step guide outlining tips for the protection against and recovery from ransomware. Keywords: cybersecurity; future recovery; protect; ransomware Created Date: 20210510185841Z
Tags:
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
ITL Bulletin Guidelines for Securing Wireless Local …
csrc.nist.govWireless networks, like other communications networks, ... NIST SP 800-153, Guidelines for Securing Wireless Local Area Networks (WLANs), was
Guidelines, Network, Communication, Wireless, Inst, Bulletin, Local, Communications networks, Wireless networks, Bulletin guidelines for securing wireless local, Securing, Guidelines for securing wireless local
Windows 7 BitLocker FIPS Security Policy - NIST
csrc.nist.govWindows 7 BitLocker™ Drive Encryption is a data protection feature available in Windows® 7 Enterprise and Ultimate for client computers and in Windows Server 2008 R2. BitLocker is Microsoft’s response to one of our
An information exchange For Information Security and ...
csrc.nist.govIdentity, Credential, and Access Management ICAM ICAM represents the intersection of digital identities, credentials, and access control into one comprehensive approach.
A Random Zoo: Sloth, Unicorn and trx - NIST
csrc.nist.govsloth, described in Section 3 (and pronounced “slow th”), a new approach to public randomness selection, unicorn, is proposed in Section 4: unicorn results in a
Port Authority Series PA111-SA CDI 01-03-0912B
csrc.nist.govThe Port Authority is designed primarily to protect firewall/router console port access. The device was designed to overcome the weaknesses of RADIUS and TACACS+ for remote access authentication. The problem of the firewall/router not being able to contact
HikSSL Cryptographic Module version 1.0.0 FIPS 140-2 Non ...
csrc.nist.govHangzhou Hikvision Digital Technology Co., Ltd. affirms that the module runs correctly on the following network camera and NVR models: • Network Cameras: model names starting with DS-2CD2.
Technology, Digital, Hikvision, Hangzhou, Hangzhou hikvision digital technology
A Method for Quantitative Risk Analysis - NIST
csrc.nist.govIt does, however, present its results in a management-friendly form of monetary values, percentages, and probabilities. Since the Office of Management and ... A Method for Quantitative Risk Analysis James W. Meritt. There are two primary methods of risk analysis: Analysis.
Analysis, Management, Methods, Risks, Inst, Quantitative, Method for quantitative risk analysis
20 Most Important Controls For Continuous Cyber Security ...
csrc.nist.govTopics • Background • Philosophy and Approach for the “20 Most Important Security Controls” • Control Examples and List of Controls
J) of SP 800 - NIST Computer Security Resource Center
csrc.nist.govbetween SP 800-53, Revision 4 and the Initial Public Draft of SP 800- 53, Revision 5. The changes to the control baselines are reflected in a separate document.
Publication Number: NIST Special Publication (SP) 800-53 ...
csrc.nist.govThe Special Publication 800-series reports on ITL’s research, guidelines, and outreach efforts in information system security, and its collaborative activities …
Special, Inst, Publication, Nist special publication, Special publication 800
Related documents
Six Steps to Proper Citation Infographic, APA Style 7th ...
apastyle.apa.orgSix Steps to Proper Citation Infographic. 1. READ. the work you want to cite. 2. Identify an . IDEA. you want to put in your paper. 3. Write a . SENTENCE. about that idea. 4. Write a . REFERENCE LIST ENTRY. for the work. 5. Add the corresponding . IN-TEXT CITATION. to the sentence. 6. REPEAT. as needed for more works and ideas.
Before the age of 18 - Centers for Disease Control and ...
www.cdc.govInfographic displaying latest statistics from the National Intimate Partner and Sexual Violence Survey 2010-2012. Shows key statistics on intimate partner violence, sexual violence, rape, violence experienced before the age of 18, and resulting negative i mpacts such as feeling fearful, concern for safety and symptoms of post-traumatic stress ...
LOW INCOME - GOV.UK
assets.publishing.service.gov.ukLOW INCOME How is it measured in Households Below Average Income? 1. The Family Resources Survey is carried out with a sample of approximately 20,000 households around the UK
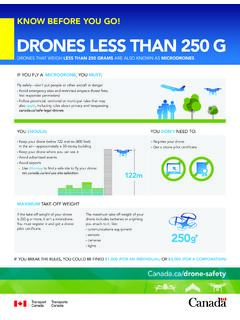
KNOW BEFORE YOU GO! DRONES LESS THAN 250 G
tc.canada.caKNOW BEFORE YOU GO! DRONES LESS THAN 250 G DRONES THAT WEIGH LESS THAN 250 GRAMS ARE ALSO KNOWN AS MICRODRONES. IF YOU FLY A MICRODRONE, YOU MUST: YOU SHOULD: MAXIMUM TAKE-OFF WEIGHT • Register your drone • Get a drone pilot certificate YOU DON’T NEED TO: If the take-off weight of your drone is 250 g or more, it isn’t a …
Than, Know, Before, Less, Drones, Know before you go, Drones less than
REDUCE THE SPREAD OF COVID-19. WASH YOUR HANDS. - …
www.canada.ca2 Apply soap REDUCE THE SPREAD OF COVID-19. WASH YOUR HANDS. 1-833-784-4397 canada.ca/coronavirus phac.info.aspc@canada.ca 5 Dry hands well with paper towel
FROSTBITE & HYPOTHERMIA - Centers for Disease Control …
www.cdc.govCS253565-A AVOID SPOT. TREAT . FROSTBITE & HYPOTHERMIA. In cold temperatures, your body begins to lose heat faster than it can be produced, which can lead to …
OFFICE OF FEDERAL CONTRACT COMPLIANCE PROGRAMS …
www.dol.govJURISDICTIONAL THRESHOLDS EXECUTIVE ORDER 11246 SUPPLY & SERVICE Basic Coverage Any number of employees + Contracts more than $10,000. AAP Coverage. 50. or more
VETERAN POPULATION - Veterans Affairs
www.va.govAnnual % Change of Veteran Population Over 30 Years Total Male Female VetPop2016 -1.8% -2.2% (Blue) +0.6% (Red) 1 20.8M 12.0M National Center for Veterans Analysis and Statistics May 3, …