Criminal Justice Information Services (CJIS) Security Policy
Jun 01, 2019 · Section 5.13.2 Mobile Device Management (MDM): add exception to the MDM requirement for indirect access, Fall 2018, APB#14, SA#2, Mobile Device Management. 13.
Policy, Services, Information, Devices, Security, Mobile, Management, Criminal, Justice, Cjis, Criminal justice information services, Security policy, Mobile device management
Download Criminal Justice Information Services (CJIS) Security Policy
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
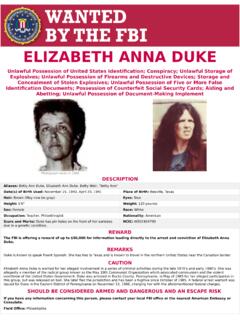
ELIZABETH ANNA DUKE - FBI
www.fbi.govPhotograph taken in 1985 ELIZABETH ANNA DUKE Unlawful Possession of United States Identification; Conspiracy; Unlawful Storage of Explosives; Unlawful Possession of Firearms and Destructive Devices; Storage and
reCenT InsIder THeFT CAses U.S. Department of Justice ...
www.fbi.govThat insider may steal solely for personal gain, or that insider may be a “spy”—someone who is stealing company information or products in order to benefit another organization or country.
NatioNal GaNG iNtelliGeNce ceNter - FBI
www.fbi.govthe gang estimates presented in the 2011 National Gang threat assessment (NGta) represents the collection of data provided by the National Drug intelligence Center (NDiC) – through the
Assessment, Threats, National, Gang, National gang threat assessment
The FBI Ofice for Victim Assistance Victim Specialists ...
www.fbi.govVictim Specialists to provide assistance to victims of crimes investigated by the FBI. Types of Federal crimes where the FBI Victim Assistance Program and/or Victim
Assistance, Specialists, Victims, For victim assistance victim specialists
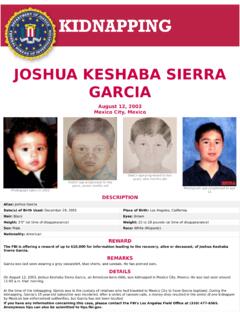
JOSHUA KESHABA SIERRA GARCIA - Welcome to FBI.gov
www.fbi.govOn August 12, 2003, Joshua Keshaba Sierra Garcia, an American-born child, was kidnapped in Mexico City, Mexico. He was last seen around 11:00 a.m. that morning.
Sierra, Joshua, Garcia, Joshua keshaba sierra garcia, Keshaba
INTERROGATION BEST PRACTICES HIGH-VALUE DETAINEE ... …
www.fbi.gov1 I. Introduction The National Defense Authorization Act for Fiscal Year 2016 requires the High-Value Detainee Interrogation Group (HIG) to submit a report on best practices for interrogation.1 ...
High, Practices, Best, Best practices, Value, Group, Interrogation, Detainees, High value detainee interrogation group
Law Enforcement Cyber Incident Reporting - FBI
www.fbi.govCyber Incident Reporting A Unified Message for State, Local, Tribal, and Territorial Law Enforcement Cyber threats from malicious actors are a growing concern across the United States.
Enforcement, Reporting, Cyber, Incident, Incident reporting, Law enforcement cyber incident reporting
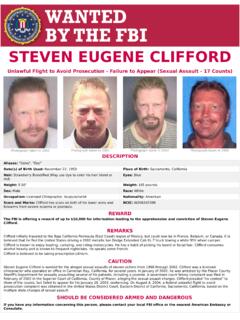
STEVEN EUGENE CLIFFORD - Welcome to FBI.gov
www.fbi.govSteven Eugene Clifford is wanted for the alleged sexual assaults of eleven victims from 1998 through 2002. Clifford was a licensed chiropractor who operated an office in Carnelian Bay, California ...
QUALITY ASSURANCE STANDARDS FOR FORENSIC DNA …
www.fbi.govQuality Assurance Standards for Forensic DNA Testing Laboratories Effective September 1, 2011 Competency test(s) is a written, oral and/or practical test or series of tests, designed to establish ...
Standards, Quality, Assurance, Forensic, Quality assurance standards for forensic
Active Shooter Incidents in the United States in 2016 and 2017
www.fbi.govIntroduction The FBI has designated 50 shootings in 2016 and 2017 as active shooter incidents. Twenty incidents occurred in 2016, while 30 incidents occurred in 2017.
Related documents
Zscaler Client Connector
www.zscaler.comZscaler Client Connector supports most device types, including laptops, smartphones, tablets, POS systems, and RF scanners (mobile computers) on platforms such as iOS, Android, Windows, MacOS, CentOS 8, and Ubuntu 20.04. Zscaler Client Connector (formerly Zscaler App or Z App) is a lightweight application deployed on the end-user device that
VMware Workspace ONE Editions Comparison Table
www.vmware.comConfigure mobile device management (MDM) policies, settings and device configurations across phones, tablets and laptop devices that run iOS, …
Devices, Mobile, Management, Policies, Vmware, Mobile device management
Workspace ONE Unified Endpoint Management - VMware
www.vmware.comWorkspace ONE UEM reinvents device hygiene by addressing security on multiple fronts and providing rich management controls that allow admins to customize an array of security policies and device posture checks. • Built-in features for system settings, data protection, apps, device controls, and more can restrict
Deploy an endpoint detection and response (EDR) solution ...
download.microsoft.comMicrosoft Endpoint Manager is a unified endpoint management and security platform, including the features and functionality delivered by Configuration Manager and Microsoft Intune Microsoft Intune Microsoft Intune is a cloud-based service that focuses on mobile device management (MDM) and mobile application management (MAM).
Incident Reporting - United States Army
armypubs.army.milor imminent threat of violation of security policies, security procedures, or acceptable use policies. Treat evidence or suspicion of an incident, intrusion, or criminal activity with care, and maintain the IS without change, pending coordination …
United, States, Reporting, Policies, Army, United states army
PK-Enabling Mobile Devices with DoD PKI Credentials
dl.dod.cyber.mil• Key management server and set of apps for mobile devices • Aims to facilitate separating key management from device management Key management maintains affinity with PKI and is used across the enterprise Device management can …
Draft NIST SP 800-124 Rev. 2, Guidelines for Managing the ...
nvlpubs.nist.gov199 mobile device management technologies, the security capabilities currently available for laptops 200 are different than those available for smartphones, tablets, and other mobile device types. 201 Further, mobile devices contain features not generally available in laptops (e.g., multiple wireless
Devices, Mobile, Management, Mobile devices, Mobile device management
Intune Mobile Application Management without …
www.herricktechlabs.comIntune Mobile Device Management Without Enrollment (MAM-WE) Outlook for iOS and Android is fully architected in the Microsoft Cloud and meets the security and compliance requirements needs of all United States Government customers when the mailboxes reside in Exchange Online.
Devices, Applications, Mobile, Management, Without, Mobile device management, Intune, Intune mobile application management without