Criminal Justice Information Services (CJIS) Security Policy
Jun 01, 2019 · The CJIS Security Policy provides a secure framework of laws, standards, and elements of published and vetted policies for accomplishing the mission across the broad spectrum of the criminal ...
Policy, Services, Information, Security, Criminal, Justice, Secure, Cjis, Criminal justice information services, Security policy
Download Criminal Justice Information Services (CJIS) Security Policy
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
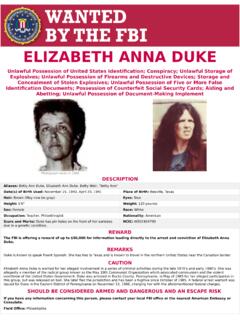
ELIZABETH ANNA DUKE - FBI
www.fbi.govPhotograph taken in 1985 ELIZABETH ANNA DUKE Unlawful Possession of United States Identification; Conspiracy; Unlawful Storage of Explosives; Unlawful Possession of Firearms and Destructive Devices; Storage and
reCenT InsIder THeFT CAses U.S. Department of Justice ...
www.fbi.govThat insider may steal solely for personal gain, or that insider may be a “spy”—someone who is stealing company information or products in order to benefit another organization or country.
NatioNal GaNG iNtelliGeNce ceNter - FBI
www.fbi.govthe gang estimates presented in the 2011 National Gang threat assessment (NGta) represents the collection of data provided by the National Drug intelligence Center (NDiC) – through the
Assessment, Threats, National, Gang, National gang threat assessment
The FBI Ofice for Victim Assistance Victim Specialists ...
www.fbi.govVictim Specialists to provide assistance to victims of crimes investigated by the FBI. Types of Federal crimes where the FBI Victim Assistance Program and/or Victim
Assistance, Specialists, Victims, For victim assistance victim specialists
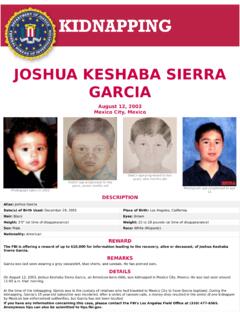
JOSHUA KESHABA SIERRA GARCIA - Welcome to FBI.gov
www.fbi.govOn August 12, 2003, Joshua Keshaba Sierra Garcia, an American-born child, was kidnapped in Mexico City, Mexico. He was last seen around 11:00 a.m. that morning.
Sierra, Joshua, Garcia, Joshua keshaba sierra garcia, Keshaba
INTERROGATION BEST PRACTICES HIGH-VALUE DETAINEE ... …
www.fbi.gov1 I. Introduction The National Defense Authorization Act for Fiscal Year 2016 requires the High-Value Detainee Interrogation Group (HIG) to submit a report on best practices for interrogation.1 ...
High, Practices, Best, Best practices, Value, Group, Interrogation, Detainees, High value detainee interrogation group
Law Enforcement Cyber Incident Reporting - FBI
www.fbi.govCyber Incident Reporting A Unified Message for State, Local, Tribal, and Territorial Law Enforcement Cyber threats from malicious actors are a growing concern across the United States.
Enforcement, Reporting, Cyber, Incident, Incident reporting, Law enforcement cyber incident reporting
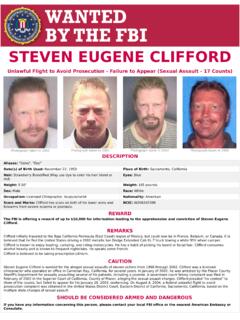
STEVEN EUGENE CLIFFORD - Welcome to FBI.gov
www.fbi.govSteven Eugene Clifford is wanted for the alleged sexual assaults of eleven victims from 1998 through 2002. Clifford was a licensed chiropractor who operated an office in Carnelian Bay, California ...
QUALITY ASSURANCE STANDARDS FOR FORENSIC DNA …
www.fbi.govQuality Assurance Standards for Forensic DNA Testing Laboratories Effective September 1, 2011 Competency test(s) is a written, oral and/or practical test or series of tests, designed to establish ...
Standards, Quality, Assurance, Forensic, Quality assurance standards for forensic
Active Shooter Incidents in the United States in 2016 and 2017
www.fbi.govIntroduction The FBI has designated 50 shootings in 2016 and 2017 as active shooter incidents. Twenty incidents occurred in 2016, while 30 incidents occurred in 2017.
Related documents
Aruba ClearPass Policy Manager Data Sheet
www.arubanetworks.comAruba’s ClearPass Policy Manager, part of the Aruba 360 Secure Fabric, provides role- and device-based secure network access control for IoT, BYOD, corporate devices, as well as employees, contractors and guests across any multivendor wired, wireless and VPN infrastructure. With a built-in context-based policy engine, RADIUS,
Policy, Manager, Secure, Clearpass policy manager, Clearpass
Ciphertext-Policy Attribute-Based Encryption
www.cs.utexas.edusecure against collusion attacks. Previous Attribute-Based Encryption systems used attributes to describe the encrypted data and built policies into user’s keys; while in our system attributes are used to describe a user’s credentials, and a party encrypting data deter-mines a policy for who can decrypt. Thus, our meth-
Policy, Based, Encryption, Secure, Attribute, Ciphertext policy attribute based encryption, Ciphertext
SAMPLE FINANCIAL MANAGEMENT POLICY AND PROCEDURES
www.hud.govMay 03, 2016 · This policy and any later changes shall be submitted to the [Tribal Council or Board of Commissioners] (“Board”) for approval. The Council/B oard is responsible for ... • Records are maintained and stored in a manner that is secure and accessible through the retention period; • Appropriate safeguards are in place against illegal access ...