Search results with tag "Encryption"
Advanced Encryption Standard (AES)
www.cse.wustl.eduAdvanced Encryption Standard (AES) Keywords: Advanced Encryption Standard (AES), Basic Structure of AES, 1. Substitute Bytes, 2. Shift Rows, 3. Mix Columns, AES Arithmetic, 4. Add Round Key, AES Key Expansion, AES Example Key Expansion, AES Example Encryption, AES Example Avalanche, AES Decryption, Homework 5 Created Date: 9/14/2011 2:45:30 AM
Somewhat Practical Fully Homomorphic Encryption
eprint.iacr.orgFully homomorphic encryption (FHE) allows evaluation of arbitrary functions on encrypted data, and as such has a myriad of potential applications such as private cloud computing. Gentry [7,8] was the rst to show that FHE is theoretically possible. His construction consisted of three parts: rst, construct an encryption scheme that is
VMWARE vSPHERE VIRTUAL MACHINE ENCRYPTION
www.vmware.comRather than looking to that layer to provide security services, existing encryption solutions try to take the same approach one would take with a laptop or bare metal server . This requires modifications to the ... encryption is handled at the host, data does not travel in the clear at all .
Homomorphic Encryption for Arithmetic of Approximate …
eprint.iacr.orgKeywords. Homomorphic encryption, approximate arithmetic 1 Introduction Homomorphic encryption (HE) is a cryptographic scheme that enables homomorphic oper-ations on encrypted data without decryption. Many of HE schemes (e.g. [18, 6, 7, 4, 5, 25, 33, 2, 26, 13, 12, 21, 19]) have been suggested following Gentry’s blueprint [23]. HE can be
Secret-Key Encryption Lab
www.cs.dartmouth.eduMost of the encryption modes require an initial vector (IV). Properties of an IV depend on the cryptographic scheme used. If we are not careful in selecting IVs, the data encrypted by us may not be secure at all, even though we are using a secure encryption algorithm and mode. The objective of this task is to help you
NFS best practice and implementation guide | TR-4067 - …
www.netapp.com• NetApp Aggregate Encryption (NAE) • Self-encrypting Drives (SED) • NetApp Storage Encryption Drives (NSE) • Export Policies and Rules • Access control lists (ACLs) • Identity management (users, groups, file ownership) • Kerberos (krb5, krb5i, krb5p) − Supported encryption types include: AES-256, AES-128, 3DES, DES
Trust Dies in Darkness: Shedding Light on Samsung’s …
eprint.iacr.orgThe Advanced Encryption Standard (AES) is the most widely used symmetric block cipher. Galois Counter Mode (GCM) is a mode of operation for block ciphers that provides Authen-ticated Encryption. AES-GCM is a stream cipher that uses AES-CTR (Counter Mode) and the Galois Message Authenti-cation Code (GMAC) internally.
The science of encryption: prime numbers and mod arithmetic
math.berkeley.eduThe science of encryption: prime numbers and mod n arithmetic Go check your e-mail. You’ll notice that the webpage address starts with \https://". The \s" at the end stands for \secure" meaning that a process called SSL is being used to encode the contents of your inbox and prevent people from hacking your account. The heart of SSL { as well
Recommendation for block cipher modes of operation ... - NIST
nvlpubs.nist.govauthenticated encryption with associated data. GCM is constructed from an approved symmetric key block cipher with a block size of 128 bits, such as the Advanced Encryption Standard (AES) algorithm that is specified in Federal Information Processing Standard (FIPS) Pub. 197 [2]. Thus, GCM is a mode of operation of the AES algorithm.
America’s Seed Fund powered by the National Science …
seedfund.nsf.govCA5. Encryption, including Homomorphic Encryption CA6. Network and Device Security CA7. Personal Authentication CA8. Secure and Trusted Computing CA9. Secure Machine-to-Machine Communication CA10. Security of Cloud and HPC Platforms CA11. Other Cybersecurity and Authentication Technologies
IBM FlashSystem 9200 Product Guide
www.redbooks.ibm.comAdvanced Encryption Standard (AES), data at rest encryption with all NVMe type drives, and IBM FlashCore Modules drives with FIPS 140-2. In-line hardware compression with IBM FlashCore Module type drives Tiering or mirroring to existing storage Mixed workload consolidation Nondisruptive data migrations Concurrent code load
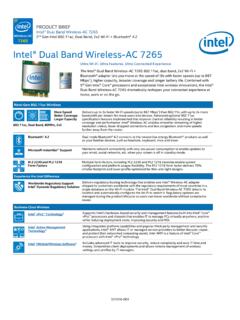
Intel® Dual Band Wireless-AC 7265 Brief
www.intel.comEncryption 64-bit and 128 -bit WEP, AES -CCMP, TKIP Wi-Fi Direct* Encryption and Authentication WPA2, AES -CCMP Product Safety Management Frame Protection UL, C-UL, CB (IEC 60950 -1) 802.11w (WFA- Protected Management Frames)
Management of Native Encryption - McAfee
www.mcafee.coman open platform, MVISION ePO or McAfee ePO software enable you to connect your security solutions to your enterprise infrastructure to increase visibility, gain efficiencies, and strengthen protection. Management of native encryption is deployed in the same method as all McAfee software. First, the agent
McAfee MVISION Cloud
www.mcafee.comEncryption Protects sensitive data with peer-reviewed, function preserving encryption schemes using customer-controlled keys for structured and unstructured data. Information Rights Management Applies rights management protection to files uploaded to or downloaded from cloud services, ensuring sensitive data is protected anywhere.
Integrity and Data Encryption (IDE) ECN Deep Dive
pcisig.comEncryption (IDE) •Goals: Provide confidentiality, integrity, and replay protection for PCIe Transaction Layer Packets (TLPs) •Support wide variety of use models •Broad interoperability •Aligned to industry best practices & extensible •Security model - Physical attacks on Links, to read confidential data, modify TLP contents, & reorder
RSA Public-Key Encryption and Signature Lab
seedsecuritylabs.orgRSA (Rivest–Shamir–Adleman) is one of the first public-key cryptosystems and is widely used for secure communication. The RSA algorithm first generates two large random prime numbers, and then use them to generate public and private key pairs, which can be used to do encryption, decryption, digital signature
Enabling and Disabling eDrive to Utilize Hardware Encryption
media.kingston.comDrives> Configure use of hardware-based encryption for fixed data drives (Enable and then Apply) 4. Use the Windows Key to search for Manage BitLocker and then run the application. 5. Select Turn on BitLocker from within the Explorer window. 8 6. Continue through the prompts to configure the target SSD.
Homomorphic Encryption - Shai Halevi
shaih.github.ioHomomorphic encryption provides an elegant solution to this conundrum. The company can keep the information in the cloud in encrypted form, and the cloud provider can process the information in this form and send only the processed result back to the company to be decrypted.
A FULLY HOMOMORPHIC ENCRYPTION SCHEME A …
crypto.stanford.edua fully homomorphic encryption scheme a dissertation submitted to the department of computer science and the committee on graduate studies of stanford university
Oracle Cloud Infrastructure Security Architecture
www.oracle.comData Encryption 12 API Security 12 Culture of Trust and Compliance 12 Development Security 12 Personnel Security 13 Supply-Chain Security 13 Compliance 13 Auditing 13 ... The design of the physical layer is a simple, flat network connected to virtual ports on …
DS-7600NI-K2/P Series NVR
www.hikvision.comAug 11, 2021 · H.265+ compression effectively reduces the storage space by up to 75% Dual-OS design to ensure high reliability of system running Adopt stream over TLS encryption technology which provides more secure stream transmission service HD Video Output Provide independent HDMI and VGA outputs HDMI video output at up to 4K resolution
Xerox AltaLink Color Multifunction Printers
www.office.xerox.comPermissions, Configuration Watchdog, TPM, Trusted Boot, Encrypted Storage Drive (AES 256-bit, FIPS 140-2), Job Level Encryption via HTTPS and Drivers, Signed Email, Common Criteria Certification (ISO 15408), Encrypted Secure Print, Imaging Security (copy, print, scan, email) with AltaLink’s proprietary marking and infrared
PRECISION 3240 COMPACT The smallest workstation with AI ...
www.delltechnologies.comCrypto Accelerator, Microsoft Windows Bitlocker, Local HDD data wipe via BIOS (“Secure Erase”), Encryption - SED HDD (Opal FIPS), Chassis lock slot support, Chassis Intrusion Switch, D-Pedigree (Secure Supply Chain Functionality), Setup/BIOS Password, Optional Smart Card keyboards, Optional Smart Card Reader, Intel ®
Ciphertext-Policy Attribute-Based Encryption
www.cs.utexas.edutonic “access tree”, where nodes of the access struc-ture are composed of threshold gates and the leaves describe attributes. We note that AND gates can be constructed as n-of-nthreshold gates and OR gates as 1-of-nthreshold gates. Furthermore, we can handle more complex access controls such as numeric ranges
DS-7700NI-K4 Series NVR
www.hikvision.comAug 11, 2021 · H.265+ compression effectively reduces the storage space by up to 75% Dual-OS design to ensure high reliability of system running Adopt stream over TLS encryption technology which provides more secure stream transmission service HD Video Output Provide independent HDMI and VGA outputs HDMI video output at up to 4K resolution
Signing, Sealing and Electronically Transmitting Documents
www.ncbels.orgthrough powerful encryption and public key infrastructure (PKI) support. Using Acrobat, you can sign and certify PDF files using a higher assurance digital signature verified by a . trusted third-party certificate authority through the purchase of a digital ID. Recipients can then use Acrobat or free Adobe Reader software to
DoD CAC Signature Certificate: Locating the Principal Name ...
www.dau.eduNov 24, 2021 · Signature - SPENCER.C... Encryption - SPENCER.C... Tasks View My Certificate Tasks View this certificate... Delete this certificate Importa certificate... Export this certificate... Smart Card Tasks Show my smart card info Help Tasks Get help on using this software g Ready SPENCER.C„. DOD ID CA-59 CAP NUM SC
Data Delivery Standards - SEC
www.sec.gov11. All electronic productions submitted on media must be produced using industry standard self -extracting encryption software. 12. The SEC uses 7zip to access compressed files. Note that the SEC cannot accept files that use AES-256 Jpeg or pkAES-256-Cert Deflate compression methods, even if the files are created with 7zip.
What do I need to do when I am asked to ... - NHS Resolution
resolution.nhs.ukGeneral principles of disclosure Disclosure requests can include requests for many different types of documents and information. The most common disclosure request, however, will be for medical ... efficient but appropriate encryption and/or other data security should be used. You should also make sure that the patient is able to receive the ...
Understanding Layer 2, 3, and 4 Protocols
ptgmedia.pearsoncmg.comThe Presentation layer is used to provide a common way for applications (resid-ing at the Application layer) to translate between data formats or perform encryption and decryption. Mechanisms to convert between text formats such as ASCII and Unicode may be considered part of the Presentation layer, along
Eliminating Obsolete Transport Layer Security (TLS ...
media.defense.govJan 05, 2021 · The National Security Agency (NSA) emphatically recommends replacing obsolete protocol configurations with ones that utilize strong encryption and authentication to protect all sensitive information. Over time, new attacks against Transport Layer Security (TLS) and the algorithms it uses have been discovered.
Cloud and Identity and Access Management - Deloitte
www2.deloitte.comcomplex access control policy management, and lack of standards-driven authentication ... enforce security policies like data encryption and MFA. Conditional access policy can ... native threat intelligence service (Amazon GuardDuty) for log correlation across the ...
Lecture 5 - Cryptography - Pennsylvania State University
www.cse.psu.eduData Encryption Standard (DES) • Introduced by the US NBS (now NIST) in 1972 • Signaled the beginning of the modern area of cryptography • Block cipher – Fixed sized input • 8-byte input and a 8-byte key (56-bits+8 parity bits)
SecureML: A System for Scalable Privacy-Preserving …
eprint.iacr.orgmultiplication triplets, we propose and implement two solutions based on linearly homomorphic encryption (LHE) and oblivious transfer. The techniques are inspired by prior work (e.g., [17]) but are optimized for our vectorized scenario where we need to compute multiplication of shared matrices and vectors.
Zero Trust Maturity Model - download.microsoft.com
download.microsoft.comprotection, end-to-end encryption, monitoring, and analytics should be employed. Data Ultimately, security teams are focused on protecting data. Where possible, data should remain safe even if ... and follows least privilege access principles. Building …
Lightweight Cryptography for the Internet of Things
iab.orgBlock ciphers. Since the Advanced Encryption Standard (AES) was selected, many block ciphers with lightweight properties have been proposed. Among them, CLEFIA [8] and PRESENT [3] are well-studied about their security and implementation. Both algorithms are under consideration in ISO/IEC 29192 “Lightweight Cryptography”.
Fully Homomorphic Encryption without Bootstrapping - IACR
eprint.iacr.orgring of integers mod qand nis a large dimension, whereas in the Ring LWE instantiation, Ris the ring of polynomials over integers mod qand an irreducible f(x), and the dimension n= 1. 4We note that bootstrapping lazily – i.e., applying the refresh procedure only at …
Sample Question Paper (Term 1) Class: X Session: 2021-22 ...
cdn1.byjus.com12 Preeti needs to send a very confidential message to her colleague in office over a secure channel. She uses a technique wherein an actual message (which is in readable form) can be converted into an unreadable message. This concept is known as_____ a. Encryption b. Decryption c. Plagiarism d. Data Security.
Application Layer Functionality and Protocols
ptgmedia.pearsoncmg.comEncryption of the data for transmission and decryption of data upon receipt by the des-tination Presentation layer implementations are not typically associated with a particular protocol stack. The standards for video and graphics are examples. Some well-known standards for video include QuickTime and Motion Picture Experts Group (MPEG).
Heart Disease Prediction using Machine Learning
www.ijert.orgclassification algorithms were compared. Decision tree algorithm had the highest accuracy. Anjan Nikhil Repaka, ea tl., proposed a system in [4] that uses NB (Naïve Bayesian) techniques for classification of dataset and AES (Advanced Encryption Standard) algorithm for secure data transfer for prediction of disease. Theresa Princy.
Chapter 7 The Advanced Encryption Standard (AES)
www.facweb.iitkgp.ac.inversion is used, the name of the standard is modified to AES-128, AES-192 or AES-256 respectively. As well as these differences AES differs from DES in that it is not a feistel structure. Recall that in a feistel structure, half of the data block is used to modify the other half of the data block and then the halves are swapped. In this case
Overview of Public Key Infrastructure (PKI)
www.deaecom.govthe same key is used for both encryption and decryption. The two keys are the public key and the private key, and either can encrypt or decrypt data. A user gives his or her public key to other users, keeping the private key to him or herself. Data encrypted with a public key can be decrypted only with the corresponding private key, and vice versa.
FIPS 197, Advanced Encryption Standard (AES) - NIST
csrc.nist.govNov 26, 2001 · This standard becomes effective on May 26, 2002. 10. Patents. Implementations of the algorithm specified in this standard may be covered by U.S. and foreign patents. 11. Export Control. Certain cryptographic devices and technical data regarding them are subject to Federal export controls. Exports of cryptographic modules implementing this standard
2018 Computing Science National 5 Finalised Marking ... - SQA
www.sqa.org.ukAllow examples of compression techniques. 4. (a) 765∙2 1 (b) Mantissa – 7652 Exponent - 3 2 5. To uniquely identify a record/row in a table. 1 6. Encryption 1 7. One mark each for: round specific versions of round, for 2 or 2 decimal places or runnerAverage 2 Accept programming language example VB = math.round
How to trust and enable S/MIME certificates in ... - KeyTalk
downloads.keytalk.comPage 8 of 20 https://www.keytalk.com 6. Outlook for Android and S/MIME email encryption and digital signing Outlook for Android requires the S/MIME certificate and private key to be available in the Android certificate store.
Report on Post-Quantum Cryptography - NIST
nvlpubs.nist.govand the Advanced Encryption Standard (AES). It is not known how far these quantum advantages can be pushed, nor how wide is the gap between feasibility in the classical and quantum models. 1 NIST standardized digital signature schemes in [FIPS 186-4], as well as public key-based key establishment schemes in
FIPS 46-3, Data Encryption Standard (DES) (withdrawn May ...
csrc.nist.govOct 25, 1999 · approved methods for managing the keys used by the algorithm s specified in this standard. Public-key based protocols may also be used (e.g., ANSI X9.42). 8. Implementations. Cryptographic modules which implement this standard shall conform to the requirements of FIPS 140-1. The algorithms specified in this standard may be implemented in
Encryption: Strengths and Weaknesses of Public-key ...
www.csc.villanova.eduencryption and decryption keys as well as an algorithm for combinations of encryption and decryption keys [5]. ... been implemented in the online environment in protocols such as Secure Socket Layer (SSL) and its successor Transport Layer Security (TLS), which have been improved security in web browsing, email, and other methods of data exchange.
Similar queries
Advanced Encryption Standard, Encryption, Homomorphic Encryption, Applications, VMWARE, Layer, Homomorphic, Secure, Secure encryption, NetApp, Arithmetic, The Advanced Encryption Standard, Standard, Seed Fund, Intel, Management of native encryption, McAfee, Agent, Management, Public-Key Encryption and Signature Lab, Decryption, Computer science, Graduate studies, Oracle Cloud Infrastructure Security Architecture, Compression, Video, Xerox, Windows Bitlocker, Ciphertext-Policy Attribute-Based Encryption, Struc-ture, Signature, Certificate, Signature Certificate, Using, Principles, Security, Information, Algorithms, Cloud and Identity and Access Management, Native, Data Encryption Standard DES, SecureML: A System for Scalable Privacy-Preserving, Integers, Application Layer, Heart Disease Prediction using Machine Learning, Techniques, Encryption Standard, Data, Overview of Public Key Infrastructure, Public, Private, FIPS, NIST, Export, Report on Post-Quantum Cryptography