Search results with tag "Trusted"
Nutzungsbedingungen Trusted Shops Services
www.trustedshops.comden Trusted Shops Services profitieren Sie von den Meinungen an-derer Käufer und werden per E-Mail an die Abgabe eigener Bewer-tungen erinnert. Dies gilt für alle Online-Shops, die das Trustbadge integriert haben, um die Trusted Shops Bewertungen zu präsentieren . 2.5. Ihr persönliches Trusted Shops Konto: Loggen Sie sich in den Trus-
Intel® Desktop Boards BIOS Settings Dictionary – By Menu
www.intel.comClear Trusted Platform Module This BIOS setting is present only on Intel® Desktop Boards that include support for Trusted Platform Module (TPM). • OK • Cancel Used to clear the TPM if you are transferring ownership of the platform to a new owner. For more information, refer to your Trusted Platform Module Quick Reference Guide.
Aerohive Security Guide
docs.aerohive.comTPM Security Chip TPM (Trusted Platform Module ) is a standard cryptoprocessor from the Trusted Computing Group consortium for cryptographically securing stored data . Aerohive APs use a TPM security chip to store cryptographic keys securely
Chapter 6 - Domain 5: Security architecture and design
cdn.ttgtmedia.com† TCSEC—Trusted Computer System Evaluation Criteria, also known as the Orange Book † Trusted Computing Base (TCB)—The security-relevant portions of a computer system † Virtualization—An interface between computer hardware and the operating system, allowing multiple guest operating systems to run on one host computer INTRODUCTION
The Ancient Jewish Wedding - Jewish Jewels
www.jewishjewels.orgtrusted servant to search for a bride for his son. We see in the book of Genesis, for example, that Abraham sent his most trusted servant Eliezer (whose name means “God’s helper”) to find a wife for his son Isaac (Genesis 24:2-9). The servant found Rebekah, who became the very first Jewish bride. Eliezer was perhaps
Download and Install Java JRE 32 bit , in google type java ...
mawani.gov.saOnly Java applications identified by a certificate from a trusted authority are allowed to run, and only if the certificate can be verified as not revoked. e) High Java applications identified by a certificate from a trusted authority are allowed to run, even f the revocation status of the certificate cannot be verified. Exception Site List
Governance Framework for Trusted Electronic Health ...
www.healthit.govThe Governance Framework for Trusted Electronic Health Information Exchange (the Governance Framework) is intended to serve as the Office of the National Coordinator for Health Information Technology’s (ONC’s) guiding principles on HIE governance.
A guide to establishing a family office - Citi Private Bank
www.privatebank.citibank.comattentions and expectations of others who seek the principal’s time, support, or capital. A family office allows for the management of family matters in a structure of near complete confidentiality. Knowledge of personal information can be restricted to trusted employees, who in turn can serve as a liaison with
McAfee Application Control
www.mcafee.comOracle Enterprise Linux 5, 6, 7 ... your systems up to date using trusted users, certificates, processes, and directories. McAfee Application Control also prevents whitelisted applications from being exploited via memory buffer overflow attacks on Microsoft Windows 32- …
TWELVE STEPS and TWELVE TRADITIONS
portlandeyeopener.comour group conscience. Our leaders are but trusted servants; they do not govern. ” Where does A.A. get its direction? Sole authority in A.A. is loving God as He may express Himself in the group conscience. Formation of a group. Growing pains. Rotat-ing committees are servants of the group. Leaders do not govern, they serve. Does A.A. have a ...
HP ProLiant ML110 G7 Server
www.hp.comThe optional trusted platform module (TPM) is an added advantage that brings further security to your IT architecture. Support for an energy‑efficient redundant power supply (RPS) and integrated HP Integrated Lights‑Out 3 (iLO 3) remote management software brings down operational expenses by reducing the number of physical visits to
Preuzimanje i instaliranje sertifikata PKS CA
api.pks.rsU zavisnosti za koji ste sertifikat pokrenuli instalaciju, birate foldere. - Ukoliko ste pokrenuli PKSCAClass1.crt ili PKSCACloud.crt, birate folder Intermediate Certification Authorities. - Ukoliko ste pokrenuli PKSCARoot.crt, birate folder Trusted Root Certification Authorities. Nakon odabira foldera kliknuti Ok i izabrati Next.
2021 Value of an Advisor Study - Russell Investments
russellinvestments.comguidance a trusted human advisor can offer. The formula we created is designed to categorize the areas of value creation in a repeatable, memorable way: A Active rebalancing of investment portfolios > We believe is greater than Your fee the annual advisory fee you charge clients + B Behavioral coaching + C Customized client experience & planning +
Production Chokes - NOV Inc.
www.nov.com• Other industrial applications. ... the job done right, with trusted products you can depend on—the first time, on time, every time. 2) Plug & Cage– a plug on the tip of a stem travels up and down ... meant to reduce the torque necessary for operation, allow for fine control, low noise, while withstanding severe erosion service.
Powerful Network of The Most Powerful Women
join.chief.compersonal board of advisors. to facilitate power conversations and lead the group in constructive peer-coaching. to problem-solve, develop self-awareness, hone your leadership acumen, and normalize shared challenges. An experienced executive coach A personal board of advisors A confidential and trusted space
A Guide to Local Services in NA
www.na.orgtrusted servants. 5. For each responsibility assigned to the service structure, a single point of decision and accountability should be clearly defined. 6. Group conscience is the spiritual means by which we invite a loving God to influence our decisions. 7. All members of a service body bear substantial responsibility for
Dell EMC PowerEdge VRTX Technical Guide
i.dell.comTrusted Platform Module (TPM) The TPM is used to generate/store keys, protect and authenticate passwords, and create/store digital certificates. It also supports the Intel Xeon TXT functionality. TPM can also be used to enable the BitLocker™ hard drive encryption feature in Windows Server 2008. TPM 1.2 is supported. No
Windows 10 Minimum Hardware Requirements
download.microsoft.comAdded TechNet article for TPM 1.2 and 2.0 version comparisons Security IoT Section 5.4 Trusted Platform Module Changed TPM to be implemented and enabled on all new Windows 10 Mobile Enterprise editions based on IoT Mobile licensing for all new devices and platforms by July 28, 2016 and added clarification all devices must be in compliance with ...
The ServiceNow Configuration Management Database
www.servicenow.comchallenges. Instead of creating a trusted repository for configuration item (CI) data, CMDB initiatives often result in limited business value and unrewarded effort . The ServiceNow solution The ServiceNow®Configuration Management Database is an easy-to-use, cloud-based single system of record for your IT infrastructure and digital service data.
Group Trusted Servants: Roles & Responsibilities
www.na.orgRoles and Responsibilities Service is an essential part of recovery in Narcotics Anonymous. Most of us would never have found recovery if not for the work of members who came before us. Now free from active addiction, we too can serve the fellowship. NA service begins in the groups, which carry the message directly to still-suffering addicts.
The Art of Feedback: Giving, Seeking and Receiving …
www.cmd.act.gov.au» seeking advice or guidance from a mentor, trusted adviser or the Employee Assistance Program. See performance in a whole new light www.act.gov.auperformance 5 ATPS Performance Framework Ver 1 4. During a feedback discussion • First, confirm with the other person that it is a suitable time and place.
HP ProLiant MicroServer
www.hp.comSecurity - TPM The TPM (Trusted Platform Module) is a microcontroller chip that can securely store artifacts used to authenticate the server platform. These artifacts can include passwords, certificates and encryption keys. Windows® BitLocker™ Drive Encryption (BitLocker) is a data protection feature available in Windows Server® 2008.
ACCOUNTANTS AND SMEs CREATING A SUSTAINABLE …
www.accaglobal.comAccountants as trusted advisors to SMEs can take the lead, gain influence with business owners ... Now, SMEs need to be ready and equipped to do the same due diligence. Despite the challenges, managers of many small businesses are already changing the ... found they could help others do the same. While nearly
What to do when a loved one passes away.
www08.wellsfargomedia.comwish to reach out to a lawyer, tax professional, or trusted advisor for assistance. Remember, you don’t have to do everything all at once. Prioritizing what you need to do in order of importance can help make the process more manageable. When you’re ready, we’ll be here to support you. 1
Elevator Technology Elevator ... - thyssenkrupp Elevator
storage.thyssenkruppelevator.comA trusted partner We support our customers throughout their project lifecycle, from the design to the end-of-life phase. Every step of the way, we strive to fully ... Small offices, shops, schools, worship facilities and hotels up to four stories need sensible options in elevators. The uncomplicated design
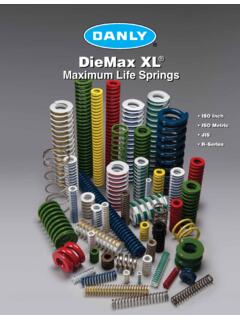
Maximum Life Springs - Dayton Lamina
www.daytonlamina.comin the tool shops of the user, or on special order at job shops. Danly brought a completely new concept into the manufacture of die sets. This was Danly’s now famous ... Danly is the name for trusted solutions and innovation for the global parts forming industry. Since 1923, Danly Delivers Quality Diemakers’ Supplies Danly Products
Department of Defense Intelligence Information System ...
www.dia.mil6) If you receive an error, it is because you do not have the DoD Root CA 2 loaded into your browser as a Trusted Certificate. You must the start over from step 11.
Step by Step - Digital IDs in Adobe Acrobat & Reader ...
entomology.k-state.eduSpecify certificate trust settings so that it can be used as a trusted root, to certify documents, and so on. Show Hidden Files and Folders in Windows 7, 8.x, and 10 . You will need Administrative rights to follow these directions. On Windows 8.x and 10 . You can use this Ribbon in . File Explorer . on the . View .
HP 200 G4 22 All-in-One PC
h20195.www2.hp.comHP Support HP PC Hardware Diagnostics HP Cloud Recovery HP Support Assistant Internet Security and Antivirus McAfee LiveSafe (30-day subscription)1 Product Setup HP JumpStarts Security Features Trusted Platform Module (TPM) 2.0 (firmware)2,3 Productivity Xerox® DocuShare® (90 days free trial offer)4 3. In selected countries, machines pre
PAPER V BASIC PRINCIPLES OF MARKETING AND …
ddegjust.ac.inlaughs. The job of marketers is to 'think customer' and to guide companies to develop offers that are meaningful and attractive to target customers. Already sea changes have been taking place in the global economy. Old business road maps cannot be trusted. Companies are learning that it is hard to build a reputation and easy to lose it. The
Dell EMC PowerEdge R650 Spec Sheet - Dell Technologies
www.delltechnologies.comcryptographically trusted booting and silicon root of trust • Maintain server firmware safety with digitally signed firmware packages • Prevent unauthorized configuration or firmware change with system lockdown • Securely and quickly wipe all data from storage media, including hard drives, SSDs and system memory with System Erase Spec Sheet
Go to www.us.army.mil to register for an AKO account ...
www.jagcnet.army.milTrusted sites YOU ARE ACCESSING A U.S. GOVERNMENT (USG) INFORMATION SYSTEM (IS) THAT IS PROVIDED FOR USG-AUTHORIZED USE ONLY. ay using this IS (which includes any device attached to this IS), you consent to the fallowing conditions: The USG routinely intercepts and monitors communications an this IS far purposes including,
Building America: Contributions of African American Slaves
uh.edurespected and trusted him. James Beckwourth, a runaway slave from St. Louis, Missouri traveled west. He lived with the Crow Indians for a while and discovered a pass in the Sierra Nevada. This pass is located north of Reno, Nevada. Many people traveled through it on their way to California.
FAR - Aircraft Spruce
www.aircraftspruce.comreliable and trusted training materials and pilot supplies. In its 80-year journey, ASA has evolved to now provide more than 1,000 products serving students, pilots, flight instructors, aviation maintenance technicians, air traffic controllers, career aviators, remote pilots and drone operators. ASA-20-FAR-AMTPD ISBN 978-1-61954-811-4 Website
Product lines - media.crouzet.com
media.crouzet.comCrouzet is your trusted partner of choice to face industrial challenges of today and tomorrow. OUT CROUET WORLDWIDE PRESENCE NANTE S, VOUVRY, CASABL ANC A 2, VALENCE , HUIZHO U, CASAB LANC A 1, FRANCE SWITZERLAND ... Nominal torque (mN.m) 2.2 / 7.7 41 100 170 / 270 50 110 180 / 290 125 550 830 1900 10 110 2.5 8 15 300 Noise level (dBA) 55 55 …
Digital Information Technology - Edexcel
qualifications.pearson.com3 Piccalilli Shoes sells shoes through its nationwide shops and telephone orders. (a) The company records transactional data from all sales. ... was not genuine/a trusted organisation that contained a viruses (1) Clare could have downloaded an email attachment (1) which ran a malicious program (1). Accept any other appropriate response
Benchmarks Social Studies - Education Scotland
education.gov.scotcan be trusted and can use this in learning about the past. SOC 1-01a By exploring places, investigating artefacts and locating them in time, I have developed an awareness of the ways in which we remember and preserve Scotland’s history. SOC 1-02a I can use evidence to recreate the story of a place or individual of local historical interest.
Multi-Residential Metering Enclosures Brochure
www.brenclosures.com.aubusiness with the world’s leading mining companies for over 20 years. ... external) are trusted by customers as a partner who listens to ... • Lift-off door for easy installation. • Sales in NSW Supply Authority regions require GMEPLK locking handle.
Research, Innovation and Enterprise 2025 Plan - Nrf
www.nrf.gov.sgposition as a trusted digital innovation hub Renew and build a liveable, resilient, sustainable and economically vibrant city for tomorrow Better transform and protect health, advance human potential and create economic value for Singapore Leveraging R&D to reinforce Singapore’s position as a global business and innovation hub
COMMON APPLICATION TIP SHEET
www.centerville.k12.oh.usAdvisors: This is not for staff at Centerville City Schools! Counselors are not permitted to be both recommenders and advisors. This is for a professional, family member, or trusted friend who may be assisting you with your application. They can view your application, but they cannot alter or submit it. You do not have to enter an Advisor. 6.
GE Retiree Update
gecorp6.custhelp.comadvisors, and comprehensive knowledge of the Medicare market combine to make Via Benefits the trusted advisor for hundreds of thousands of retirees. Via Benefits helps you choose the health care coverage that fits your individual needs and budget. Working with us will help you make informed and confident enrollment decisions.
Financial coaching: A strategy to improve financial well-being
files.consumerfinance.govfinancial coach can serve as a capable and trusted guide to help consumers navigate those decisions, especially consumers who do not have access to professional financial advisors or to experienced financial mentors among their family and friends. Recognizing the potential of financial coaching to improve the well-being of consumers, the
TrusTed plaTform module (Tpm) Toshiba securiTy supporT œ
si.dynabook.comTrusTed plaTform module (Tpm) Trusted Platform Module (TPM) ©2006. Toshiba Europe GmbH. While Toshiba has made every effort at the time of publication to ensure the accuracy of the information provided herein, product specifications, configurations, prices, system/component/options availability are all subject to change without notice. For the
Trusted TMR System Safety Manual - Rockwell Automation
literature.rockwellautomation.comRockwell Automation Publication ICSTT-RM459I-EN-P, March 2021 Supersedes Publication ICSTT-RM459H-EN-P, December 2019 Safety Manual Original Instructions Trusted TMR System
Trusted Platform Module (TPM) TCG 1.2 / 2 - Supermicro
www.supermicro.com7 Chapter 1: Introduction B. Types of TPMs for TPM 2.0 The TPM-9665 series uses TCG 2.0 (Trusted Computing Group). The following SKUs are available: • AOM-TPM-9665V, a vertical TPM without provisioning • AOM-TPM-9665H, a horizontal TPM without provisioning • AOM-TPM-9665V-S, a vertical server-side TPM • AOM-TPM-9665H-S, a horizontal server-side TPM ...
Trusted Shops garantieverklaring
www.trustedshops.comConsumenten hebben het onderstaande ontbindingsrechtrecht. Herroepingsrecht U heeft het recht om binnen een termijn van 14 dagen zonder opgave van reden de overeenkomst te herroe-pen. De herroepingstermijn verstrijkt 14 dagen na de dag van de sluiting van de overeenkomst.
Similar queries
Trusted Shops, Shops, Intel, Desktop Boards BIOS Settings Dictionary – By, Trusted Platform Module, Platform, Trusted Platform Module Quick Reference, Trusted, Trusted Computer System Evaluation Criteria, Computer system, Computer, System, Ancient Jewish Wedding, Governance Framework for Trusted Electronic Health, Governance Framework for Trusted Electronic Health Information Exchange, Governance Framework, Office of the National Coordinator for Health Information Technology, Governance, Guide to establishing a family office, Others, McAfee, Oracle, Trusted Servants, Servants, Sertifikata, Instalaciju, Trusted root, Value of an Advisor Study, Industrial, Torque, Advisors, Guide to Local, Dell EMC PowerEdge VRTX Technical Guide, Roles, Responsibilities, Roles and Responsibilities, Feedback: Giving, Seeking and Receiving, Trusted advisors, Others do, Maximum Life Springs, Root, Guide, Aircraft Spruce, Information Technology, The world, Lift, Resilient, Sustainable, COMMON APPLICATION TIP SHEET, Trusted guide, Trusted Platform Module TPM, Rockwell Automation, TPM 2, Trusted Shops garantieverklaring, Consumenten