10 Steps to Cyber Security - NCSC.GOV.UK
Identity and access management Control who and what can access your systems and data. Data security Protect data where it is vulnerable. Logging and monitoring
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Summary of the NCSCS Security Analysis for the UK Telecoms ...
www.ncsc.gov.ukSummary of the NCSC’s security analysis for the UK telecoms sector 9 • The 5G core network uses a service-based architecture, utilising a broader range of data and services. This approach will have an increased attack surface over signalling networks and network APIs.
NCSC Cyber Security Toolkit for Boards - NCSC.GOV.UK
www.ncsc.gov.ukBoard members and Embedding cyber security into your structure and objectives. Cyber Security Toolkit for Boards 5 ... We want to keep adding to this toolkit as you encounter new cyber security challenges, so we'll need your practical experiences of the challenges and opportunities you encounter. Please let us know how
Cyber Essentials: Requirements for IT infrastructure
www.ncsc.gov.ukFigure 1: Scope of the requirements for IT infrastructure - Bring your own device (BYOD) In addition to mobile or remote devices owned by the organisation, user-owned devices which access organisational data or services (as defined above) are in scope. However, all mobile or remote devices used only for the purpose of: • native voice applications
Annual Review 2021
www.ncsc.gov.ukthe removal of more than 50,500 scams and more than 90,100 malicious URLs. > Up to 3 million additional key workers were protected from unintentionally accessing ... targeting all sectors from businesses to public services. In response, the NCSC has identified and mitigated numerous threats, whether
Cyber Essentials: Requirements for IT infrastructure
www.ncsc.gov.ukWorkspace, MDM Containers, Citrix Desktop, VDI solutions, RDP desktop. Scope Overview of the scope Assessment and certification can cover the whole of the Applicant’s IT infrastructure, or a sub-set. Either way, the boundary of the scope must be clearly
What to do if you’ve received a threatening email ...
www.ncsc.gov.ukemails in the hope that someone will pay. They'll often include technical sounding details to make the email sound convincing. It may also include a password the victim uses or has used. d Sextortion is an example of a phi shing attack, where victims receive emails that try and tric k them into doing the wrong
Phishing attacks - NCSC.GOV.UK
www.ncsc.gov.ukDealing with suspicious emails What is phishing? Make yourself a harder target Phishing is when criminals attempt to trick people into doing 'the wrong thing', such as clicking a link to a dodgy website. . Phishing can be conducted via a text message, social media, or by phone, but the term 'phishing' is mainly used to
Vulnerability Disclosure Toolkit 2 - NCSC.GOV.UK
www.ncsc.gov.ukvalidation and output encoding to all user-controlled content throughout the site to help mitigate cross-site scripting attacks. Input validation Only allow the characters you expect for the type of input you're receiving. For example: • if you expect an unsigned integer, only accept unsigned integers within the expected range
Toolkit, Vulnerability, Disclosures, Controlled, Vulnerability disclosure toolkit
Cyber Essentials: Requirements for IT infrastructure
www.ncsc.gov.ukCyber Essentials: Requirements for IT infrastructure v3.0 4 • A corporate VPN is a Virtual Private Network solution that connects back to the applicants office location or to a virtual/cloud firewall. This must be administered by the applicant
Cyclops Blink - ncsc.gov.uk
www.ncsc.gov.ukControl T1071.001 Application Layer Protocol: Web Protocols Cyclops Blink can download files via HTTP or HTTPS. Command And Control T1573.002 Encrypted Channel: ... The purpose of this module is the discovery of system information from the WatchGuard device. The module gathers a wide variety of system information, at regular intervals, by ...
Related documents
Working safely during COVID-19 restaurants pubs takeaway ...
assets.publishing.service.gov.ukor for takeaway or delivery. For example, restaurants, pubs, bars, beer gardens, food to go, cafes, self-contained hospitality which can be accessed from the outside of a closed venue, social and similar clubs operating as bars and restaurants, mobile catering and contract catering or similar environments where food and drink is purchased and
Delforno Takeaway Menu - PIZZA | PASTA
www.delforno.co.zaKIDDIES COMBO MEAL TAKEAWAY Inclu&sa se e cted kids eal PLusa kiddies SO Sg SWEET TOOTH CHOC PIZZA WAFFLES & ORDER GOURMET PASTA of n pasta at extra c PORTUGUESE TRADITIONAL of 20 ndried tomato mild peri.pen Fried falafel and patties With tomato. red onion. FAMOUS BURGERS STICKY PERI FETA Sog pure patty stuffed with feta
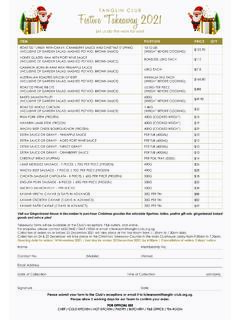
Festive Takeaway 2021 - tanglinclub.org.sg
www.tanglinclub.org.sgTakeaway forms will be available at the Club’s receptions, F&B outlets, and online. For enquiries, please contact 6622 0442 / 0443 / 0556 or email tctearoom@tanglin-club.org.sg. Collection of orders on or before 23 December 2021 will take place …
Climate Change and International Responses Increasing ...
www.dni.govKey Takeaway . We assess that climate change will increasingly exacerbate risks to US national security interests as the physical impacts increase and geopolitical tensions mount about how to respond to the challenge. Global momentum is
Qdoba Takeaway Menu - QDOBA Mexican Eats
www.qdoba.comchoose your entrÉe burrito cal 720 - ˜080 bowl cal 450 - 800 grilled quesadilla cal 920 - ˜˜90 3-cheese nachos cal 930 - ˜220 salad cal 360 - ˜270
Frozen Shoulder - American Academy of Orthopaedic …
orthoinfo.aaos.org1 Frozen Shoulder The shoulder is a complex structure that does a lot for us. The design of your shoulder helps you scratch your back, reach an item on the top shelf,
American, Shoulder, Academy, Frozen, Orthopaedic, Frozen shoulder, American academy of orthopaedic
Mathematics (Linear) 1MA0 ALGEBRA: COLLECTING LIKE TERMS
www.mathsgenie.co.ukEdexcel GCSE Mathematics (Linear) – 1MA0 ALGEBRA: COLLECTING LIKE TERMS Materials required for examination Items included with question …