FaRM: Fast Remote Memory - USENIX
shared address space and for fast messaging and is care-fully tuned for the best RDMA performance. We used FaRM to build a key-value store and a graph store simi-lar to Facebook’s. They both perform well, for example, a 20-machine cluster can perform 167 million key-value lookups per second with a latency of 31µs. 1 Introduction
Tags:
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
www.usenix.org
www.usenix.orgArchitecture and Implementation R. A. P. of Guide, an Object-Oriented Distributed System Balter, J. Bernadat, D. Decouchant, A. Duda, Freyssinet, S. Krakowiak, M ...
Guide, System, Implementation, Distributed, Object, Oriented, An object oriented distributed system
Identifying Trends in Enterprise Data Protection Systems
www.usenix.orgIdentifying Trends in Enterprise Data Protection Systems George Amvrosiadis Dept. of Computer Science, University of Toronto ... Understanding com- ... ratios Deduplication can result in the reduction of backup image sizes by more than 88%,
Identifying, Data, Protection, Understanding, Trends, Enterprise, Ratios, Deduplication, Identifying trends in enterprise data protection, Ratios deduplication
File Systems Fated for Senescence? Nonsense, Says Science!
www.usenix.organd file system design that could substantially affect ag-ing. For example, a back-of-the-envelope analysis sug-gests that aging should get worse as rotating disks get
Strangely Enough It All Turns Out Well - usenix.org
www.usenix.org• Venture Capital 101 and Building the Business • End Game – Acquisition Angst – and Assimilation • Working for Corporate America • Things I will do differently next time …. A Brief History of Softway Systems • The Mission: build an environment to allow UNIX apps to be
F Reload: A High Resolution, Low Noise, L3 Cache Side ...
www.usenix.orgFlush+Reload: A High Resolution, Low Noise, L3 Cache Side-Channel Attack ... FLUSH +RELOAD: a High Resolution, Low Noise, L3 Cache Side-Channel Attack Yuval Yarom Katrina Falkner The University of Adelaide Abstract Sharing memory pages between non-trusting processes is a common method of reducing the memory footprint of multi-tenanted systems ...
High, Noise, Resolution, Low noise, Cache, High resolution, L3 cache
Core Job Descriptions - USENIX
www.usenix.org4 / Core Job Descriptions n Ability to identify/locate shared resources and perform simple tasks (e.g., manipulate jobs in a print queue, figure out why a network file system isn’t available) n Works well alone or on a team Required Background n Two years of college …
UC San Diego On the effectiveness of mitigations …
www.usenix.orgOn the effectiveness of mitigations against floating-point timing channels David Kohlbrenner Hovav Shacham UC San Diego How effective are?
Atingsa, Points, Effectiveness, Floating, Mitigation, Timing, Channel, On the effectiveness of mitigations, On the effectiveness of mitigations against floating point timing channels
Estimating Unseen Deduplication— from Theory to Practice
www.usenix.orgment depends on the data itself and on the storage media that it resides on. The technique is based ... deduplication and data reduction in general, makes more sense than ever. Combined with the popularity of modern ... Understanding the estimation accuracy. The proofs of accuracy of the Unseen algorithm are the-
Fear the Reaper: Characterization and Fast Detection of ...
www.usenix.orgFear the Reaper: Characterization and Fast Detection of Card Skimmers Nolen Scaife University of Florida scaife@ufl.edu Christian Peeters University of Florida
Under New Management: Practical Attacks on SNMPv3
www.usenix.orgdone via SNMP, the serial port, or a web interface. Of these options, only SNMP allows for scalable configura-tion management accross a diverse group of devices. For example, a managed LAN switch can be configured with features such as port specific Quality of Service (QoS)
Related documents
Kafka: a Distributed Messaging System for Log Processing
notes.stephenholiday.comLog processing has become a critical component of the data pipeline for consumer internet companies. We introduce Kafka, a distributed messaging system that we developed for collecting and delivering high volumes of log data with low latency. Our system incorporates ideas from existing log aggregators and messaging
System, Processing, Distributed, Messaging, A distributed messaging system for log processing, Log processing, A distributed messaging system
Cloud Application Architecture Guide
info.microsoft.comasynchronous messaging or eventing. Applications scale horizontally, adding new instances as demand requires. These trends bring new challenges. Application state is distributed. Operations are done in parallel and asynchronously. The system as a whole must be resilient when failures occur. Deployments must be automated and predictable.
Examples of Commonly Used Security Safeguards
www.gov.mb.caidentifier. Anonymous identifiers allow processing of discrete person level records to analyze information across time, data sources or geographical areas for such purposes as measuring utilization, health system performance, and health outcomes or program evaluation. Encryption may be hardware or software based and is usually “key” based.
Security, System, Used, Processing, Example, Commonly, Safeguards, Examples of commonly used security safeguards
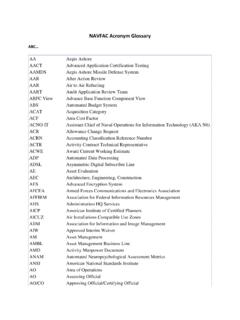
NAVFAC Acronym Glossary - Naval Facilities Engineering …
www.navfac.navy.milDUERS Defense Utility Energy Reporting System DWAS Defense Working Capital Accounting System DWAS Defense Working Capital Accounting System Earl Weapons Station Maps EBCDIC Extended Binary Coded Decimal Interchange Code EC Equipment Code ECATTS Environmental Compliance Assessment, Training, and Tracking System
System, Engineering, Naval, Facilities, Naval facilities engineering
Security Guide - Zoom
explore.zoom.usSecure log-in using standard username and password or SAML single sign-on Start a secured meeting with passcode Schedule a secured meeting with passcode Selective meeting invitation: The host can selectively invite participants via email, IM, or SMS. This provides greater control over the distribution of the meeting access information.