SYSTEM NAME AND NUMBER: DPR 39 DoD. (March 26, …
Decentralized locations include the DoD Components staff and field operating agencies, major commands, installations, and activities. ... Personal information maintained will be the minimum necessary in order to accomplish the ... Access to computerized data is restricted by use of common access cards (CACs) and
Tags:
Name, System, Data, Personal, Number, Decentralized, System name and number
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Balancing Privacy & Security: The Role of Privacy and ...
dpcld.defense.govInformation Sharing EnvironmentInformation Sharing Environment • Intelligence Reform and Terrorism Prevention Act (IRTPA) of 2004 – Sec. 1016(b)(1)(A): : The President shall create an info“The President shall create an informrmation sharing environment for the ation sharing environment for the sharing of terrorism information in a manner that is consistent with national …
THE PRIVACY ACT OF 1974 (As Amended) Public Law 93 …
dpcld.defense.gov1 THE PRIVACY ACT OF 1974 (As Amended) Public Law 93-579, as codified at 5 U.S.C. 552a Be it enacted by the Senate and House of Representatives of the United States of America in
Executive Order 12333 United States Intelligence Activities
dpcld.defense.gov(3) Threats to the United States and its interests from the development, possession, proliferation, or use of weapons of mass destruction. (e) Special emphasis shall be given to the production of timely, accurate, and insightful reports, responsive to
Destruction, Weapons, Mass, Proliferation, Of weapons of mass destruction
Introductionto* The*Privacy*Act*
dpcld.defense.govDefense Privacy and Civil Liberties Office Introduction to the Privacy Act 6 Information Sharing Concerns Need-to-Know Need-to-know is the authorized, official need ...
DOD MOBILE DEVICE SECURITY BEST PRACTICES DO DON’T
dpcld.defense.govDOD MOBILE DEVICE SECURITY BEST PRACTICES (e.g. Laptop, BlackBerry, PDA, Removable Storage Media) DON’T Use wireless headsets Use wireless hands free devices Bring wireless enabled devices into classified areas Connect a BlackBerry device to public wireless Internet access points (i.e., Hot Spots)
Related documents
Blockchain For Health Data and Its Potential Use in Health ...
www.healthit.govBlockchain is a decentralized P2P architecture with nodes consisting of network participants. Each member in the network stores an identical copy of the blockchain and contributes to the ... a public blockchain to manage and control access to personal data. IV. Bitcoin and Private Blockchain Limitations for Health Care Application
Basic Attention Token (BAT)
basicattentiontoken.orgThe solution is a decentralized, transparent digital ad exchange based on Blockchain. The rst component is Brave, a fast, open source, ... data suppliers, analytics, measurement and veri cation services to ght fraud, enhance ... lost control of how personal information is collected and used by companies."[6] A large majority, 64%, believe that ...
Operating instructions TwinSAFE Terminal with 4 digital ...
download.beckhoff.comPersonal injuries! Failure to follow this safety instruction can lead to injuries to persons. ... The Beckhoff Bus Terminal system is used for decentralized connection of sensors and actuators to a ... The E-bus is the data path within a terminal strip. The E-bus is led through from the Bus Coupler through all
Descriptive and Substantive Representation in Congress ...
lowande.polisci.lsa.umich.eduReplication Materials: The data, code, and any additional materials required to replicate all anal- ... personal bias, or constituent behavior. Nonetheless, existing studies investigate these mechanisms, and each implies a similar ... often decentralized, involving unelected bureaucrats in numerous agencies and at multiple levels of government ...
DeFi Beyond the Hype - Wharton Initiative on Financial ...
wifpr.wharton.upenn.eduDecentralized Finance (DeFi) is a developing area at the intersection of blockchain, digital assets, and financial services. DeFi protocols seek to disintermediate finance through both familiar and new service arrangements. ... Personal data subject to national privacy laws. Identity verification requirements under discussion by anti-money ...
Data, Personal, Beyond, Personal data, Hype, Decentralized, Fides, Defi beyond the hype
Relationship between Operating System, Computer Hardware ...
www.ijcttjournal.orgData security: Data is an important part of computer system. The operating system protects the data stored on the computer from illegal use, modification or deletion. Disk Management: Operating system manages the disk space. It manages the stored files and folders in a proper way. Process Management: CPU can perform one task at
Konomi: Decentralized Money Market for Cross-Chain Assets
www.konomi.networkKonomi: Decentralized Money Market for Cross-Chain Assets Konomi Foundation Abstract Konomi is a full suite asset management solution for cross-chain crypto assets. Using Substrate as the development framework, the network aims to support more assets in the Polkadot ecosystem. Users could manage their
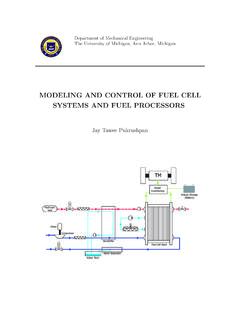
MODELING AND CONTROL OF FUEL CELL SYSTEMS AND …
www-personal.umich.eduCompany for their helpful suggestions and for providing me with valuable data on the fuel cell. I also owe a note of thanks to Larry Mianzo and Shankar Raman for allowing me to earn valuable research and work experience during my internship at Visteon Corporation. At the University of Michigan, I have worked alongside many talented students.