BIG-IP Access Policy Manager - F5
supports smart cards with credential providers, so users can connect their devices to their network before signing in. F5 partners with leading on-premises and cloud-based identity and access management (IAM) vendors, such as Microsoft, Okta, and Ping Identity. This integration enables local and
Tags:
Policy, Manager, Identity, Access, Credentials, Identity and access, Access policy manager
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Deploying the BIG-IP System with VMware Horizon View
www.f5.comF5 Deployment Guide 4 VMware Horizon View Configuration examples and traffic flows In this deployment guide, we show multiple ways of deploying the BIG-IP system with View. Specifically, if View is deployed with VMware Unified Access Gateway, the BIG-IP system can further protect, monitor, and load balance these servers, allowing PCoIP
Gain Agility with the Most Programmable Cloud …
www.f5.comHARDWARE DATASHEET BIG-IP System 2 Standardize Your App Delivery Services BIG-IP ADC appliances can simplify your network and reduce total …
Deploying the BIG-IP system with Oracle WebLogic …
www.f5.comF5 Deployment Guide Deploying the BIG-IP System with Oracle WebLogic Server Welcome to the F5 ® and Oracle WebLogic Server deployment guide. F5 provides a highly effective way to optimize and direct
Oracle, With, System, Server, Weblogic, Oracle weblogic server, Ip system with oracle weblogic, Ip system with oracle weblogic server
F5 Improves the Agility, Performance, and Security of IBM ...
www.f5.comMaximo solves these issues by optimizing Maximo delivery over the LAN and WAN, ensuring a fast, secure, and available application experience for users no matter the location or device, enabling users to remain productive.
Performance, Security, Improves, Agility, Maximo, And security, Improves the agility
Optimize Application Deployment with Cisco and F5
www.f5.comscaling of critical network and application services. The joint Cisco and F5 solution offers customers the ability to deploy and deliver applications with the speed, reliability, and security
Services, Critical, Applications, With, Cisco, Deployment, Optimize, Optimize application deployment with cisco and
BIG-IP Local Traffic Manager - F5 Networks
www.f5.com7 DATASHEET BIG-IP Local Trafic Manager More Information To learn more about BIG‑IP LTM, visit f5.com to find these and other resources. Web BIG-IP Local Traffic Manager
Navigating a Multi-Cloud World with F5
www.f5.com2 WHITE APER Navigating a ulti-loud World with F5 Contents The Transition to Cloud 3 A New Cloud Reality 3 Multi-Cloud Challenges 4 Wasn’t Cloud Supposed to Be Simple?
Multi, Cloud, World, Navigating, Navigating a multi cloud world
Guide to Updating and Upgrading BIG-IP - F5
www.f5.comF5 Deployment Guide 4 Updating or Upgrading the BIG-IP Section 1: Overview This section contains an overview of updating and upgrading your BIG-IP. Reasons to keep your BIG-IP up-to-date Our latest research on the state of applications showed that 97 percent of organizations are managing what is commonly known as
Guide, Your, Updating, Upgrading, Upgrading your, Guide to updating and upgrading big ip
VIPRION - F5
www.f5.com• High-performance interconnection between Ethernet ports and processors. • L4 offload, enabling leading throughput rates and reduced loads on software. • Hardware-accelerated SYN flood protection. • Hardware detection and mitigation of more than 100 types of denial-of-service (DoS) and DDoS attacks.
BIG‑IP Global Traffic Manager - F5
www.f5.comF5 ® BIG-IP Global Traffic Manager™ (GTM) distributes DNS and user application requests based on business policies, data center and cloud service conditions, user location, and application performance. BIG-IP GTM delivers F5’s high-performance DNS Services with visibility, reporting, and analysis; hyper-scales and secures DNS responses
Related documents
Physical Access Control Systems (PACS) Customer Ordering …
www.gsa.govFederal agencies are turning their attention to identifying and implementing changes to their physical access control systems (PACS) to support the new PIV card. This memo also required agency PACS transition plans to be in accordance with the Federal Identity, Credential, and Access Management (FICAM) Roadmap and Implementation Guidance.
Federal, Identity, Access, Credentials, Federal identity, And access
Announcing the Standard for Personal Identity Verification ...
nvlpubs.nist.govlogical access (e.g., with or without PIN, over contact, contactless, or virtual contact interface). Federal departments and agencies must use accredited issuers to issue identity credentials for Federal employees and contractors. For this purpose, NIST provided guidelines for the accreditation of PIV Card issuers in [SP 800-79].
Authentication in an Internet Banking Environment
www.ffiec.govFederal Financial Institutions Examination Council ... One method to verify a customer’s identity is a physical presentation of a proof of identity credential such as a driver's license. Similarly, to establish the validity of a business and the ... Monitoring systems can determine if unauthorized access to computer systems and customer
Federal, Identity, Access, Credentials, Authentication, Internet, Authentication in an internet, Identity credential
DoD Enterprise Identity, Credential, and Access …
dodcio.defense.govIdentity, Credential, and Access Management (ICAM) Reference Design Version 1.0 June 2020 Prepared by Department of Defense, Office of the Chief Information Officer (DoD CIO) DISTRIBUTION STATEMENT C. Distribution authorized to U.S. Government agencies and their contractors (Administrative or Operational Use).
Department of Defense
dodcio.defense.govIdentity, Credential, and Access Management (ICAM) encompasses the full range of activities related to the creation of digital Identities and maintenance of associated attributes, credential issuance for person/non-person entities, authentication, and making access management control decisions based on
Department, Defense, Identity, Access, Credentials, Department of defense, And access
REAL ID - Virginia
www.dmv.virginia.govBeginning May 3, 2023, the federal government will require you to present a REAL ID compliant credential in order to board a domestic flight. However, if you have another document accepted by the federal government, such as a U.S. passport, you can use that to board a plane or access secure federal facilities.
Digital Identity Guidelines - NIST
nvlpubs.nist.govDigital Identity Guidelines Authentication and Lifecycle Management . Paul A. Grassi James L. Fenton ... under the Federal Information Security Modernization Act (FISMA) of 2014, 44 U.S.C. § 3551 et ... 7.1.2 Access Tokens ...
Federal, Guidelines, Identity, Access, Digital, Digital identity guidelines
USE BLACK OR BLUE INK ONLY TRANSACTION TYPE • FOR …
www.dmv.ri.govREAL ID CREDENTIAL NON REAL ID CREDENTIAL REAL ID CREDENTIAL OPT-IN/OPT OUT BOX (Please select desired credential type) P.O.R. ONE _____ Note: Non REAL ID Credentials will have “NOT FOR FEDERAL IDENTIFICATION” on the card.
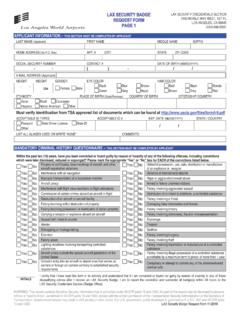
APPLICANT INFORMATION THIS SECTION MUST BE …
sbo.enroll.lawa.orgcredentials. For SIDA applications, failure to provide this information may result in denial of a credential. For other aviation credentials, although furnishing your SSN is voluntary, if you do not provide the information requested, DHS may be unable to complete your security threat assessment.