Internet Security Introduction
of information authorized users have reliable and timely access to information . Access Control p The ability to permit or deny the use of an object by a subject. ... Internet social engineering attacks packet spoofing automated probes/scans widespread denial-of-service attacks
Tags:
Information, Security, Introduction, Internet, Reliable, Internet security introduction
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
3 - TT
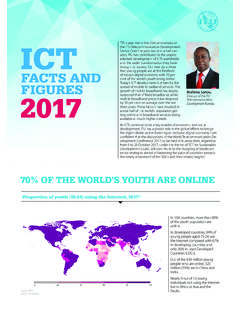
www.itu.intv The 2017 edition of the Measuring the Information Society Report was prepared by the ICT Data and Statistics Division within the Telecommunication Development Bureau of …
ICT - TT
www.itu.intFACTS AND FIGURES ICT 2017 70% OF THE WORLD’S YOUTH ARE ONLINE Proportion of youth (15-24) using the Internet, 2017* “This …
Study of Mobile Phone Usage Among the …
www.itu.intMethodology The entire primary research study was done in Mumbai and a Quantitative protocol was used. In order to provide a current snapshot of …
FINANCIAL AND REPORTING PRINCIPLES AND …
www.itu.intFINANCIAL AND REPORTING PRINCIPLES ... n Management Discussion and Analysis n Financial Results, Footnotes, and Auditor’s Opinion n Results of Corporate Operations
Analysis, Principles, Reporting, Financial, And analysis, Financial and reporting principles and, Financial and reporting principles
Business Models WG - TT
www.itu.intBusiness Models WG BM - working group Report ... These nine business model building blocks can be captured in a single diagram called the business model canvas.
Business, Model, Nacva, Business model, The business model canvas, Business models wg
Understanding cybercrime: Phenomena, challenge …
www.itu.intUnderstanding cybercrime: Phenomena, challenges and legal response iii Purpose The purpose of the ITU report Understanding Cybercrime: Phenomena, Challenges and Legal Response is
Phenomena, Challenges, Understanding, Cybercrime, Understanding cybercrime
ITU WORKSHOP ON TAXATION OF …
www.itu.intITU WORKSHOP ON TAXATION OF TELECOMMUNICATION SERVICES AND RELATED PRODUCTS ITU Headquarters Geneva, Switzerland 1-2 September 2011 CLOSING REMARKS Mario Maniewicz Dear Delegates, Ladies and Gentlemen:
Services, Product, Telecommunication, Related, Workshop, Taxation, Itu workshop on taxation of, Itu workshop on taxation of telecommunication services and related products itu
Smart Cities Seoul: a case study - TT
www.itu.intSmart Cities Seoul: a case study ... Seoul 2015” project, providing a best-practice guide to the construction and operation ... Smart cities demand careful ...
Guide, Study, Project, Smart, Case, Cities, Seoul, A case study, Smart cities, Smart cities seoul
Call to Action ICTs as a Means of Implementation …
www.itu.intCall to Action ICTs as a Means of Implementation for the Post-2015 Sustainable Development Agenda The Global e-Sustainability Initiative (GeSI) and the International Telecommunication Union
Development, Sustainable, 2015, Post, Agenda, The post 2015 sustainable development agenda
Standard ITU-T
www.itu.intITU-T www.itu.int/itu-t/studygroups The long-time leader in optical single-mode fibre and cable standardization Recommendation ITU-T G.657: "Characteristics of a ...
Related documents
Authentication in an Internet Banking Environment
www.ffiec.govin technology, the sensitivity of its customer information, and internal or external threats to information; and • Implement appropriate risk mitigation strategies. Background Financial institutions engaging in any form of Internet banking should have effective and reliable methods to authenticate customers.
Information, Authentication, Internet, Reliable, Authentication in an internet
The Role of Information Technology in E-Commerce
www.ijstr.orgThe Role Of Information Technology In E-Commerce Winwin Yadiati; Meiryani Abstract: Information technology has the power to develop the industry and transform how business is run. Internet in business is used for information exchange, media promotion, electronic mail, mailing lists, dialogue, discussions, consulting with consumers online.
Information, Technology, Commerce, Internet, Information technology in e commerce
FACTORS THAT AFFECT INFORMATION AND …
jitm.ubalt.eduInformation and communication technology (ICT) which includes radio, television and newer digital technology such as computers and the internet, are potentially powerful tools for extending educational opportunities, formal and non-formal, to one and all.
Digital divide: Improving Internet access in the ...
www.brookings.edulines, cell towers, Internet routers, wireless spectrum, reliable electricity, and the like. It is one In India, for example, smart phones run as much as $125, which is well
Introduction to TCP/IP
www.cse.wustl.eduInternet Protocol (IP)! Layer 3 protocol that forwards datagrams across internet! Uses routing tables prepared by routing protocols, e.g., Open Shortest Path First (OSPF), Routing Information Protocol (RIP)! Connectionless service vs connection-oriented (circuits)
Computer Networking: A Top-Down Approach Featuring the ...
plaza.ufl.eduDec 01, 2002 · 6. The Internet’s connection-oriented service provides reliable data transfer by using acknowledgements and retransmissions. When one side of the connection doesn’t receive an acknowledgement (from the other side of the connection) for a packet it transmitted, it retransmits the packet. 7.
Computer, Internet, Networking, Reliable, Computer networking
Digital Transformation in the Age of COVID-19
www.oecd.orgadvantage of information and communication technologies (ICTs) and the Internet to meet their public policy objectives. Through comparative evidence, it informs policy makers of regulatory practices and policy options to help maximise the potential of the digital economy as a driver for innovation and inclusive growth.
SECURITY AND PRIVACY ISSUES RELATING TO TECHNOLOGY …
www.parliament.vic.gov.authe confidential information the court may prevent disclosure using injunctive relief, the delivery up and destruction of the information or the compensation for any loss of the plaintiff arising as a result of the breach. It remains open to question whether interception of information communicated via e-mail would be deemed