Mobile Services Category Team (MSCT) Advanced Technology ...
MobileIron, AirWatch, and IBM MaaS360. Data Collection and Analysis: Mobile Threat Protection (MTP) solutions typically need to collect ... and helping remediate compromised devices, users ... The MTP solution should be capable of detecting app install events and validate the new or
Tags:
Devices, Detecting, Airwatch, Compromised, Compromised devices
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
HOW TO BUY YOUR FIRST INVESTMENT PROPERTY
s3.amazonaws.comBest-selling Books by Robert T. Kiyosaki Rich Dad Poor Dad What the Rich Teach Their Kids About Money That the Poor and Middle Class Do Not
First, Your, Property, Investment, Poor, Rich, Rich dad poor dad, Buy your first investment property
Rich Dad Poor Dad is a starting point for anyone …
s3.amazonaws.comRich Dad Poor Dad is a starting point for anyone looking to gain control of their nancial future. USA TODAY
Points, Looking, Starting, Poor, Rich, Rich dad poor dad, Starting point for anyone, Anyone, Starting point for anyone looking
deal too ig to pass up - s3.amazonaws.com
s3.amazonaws.comThe Essentials is required for all Optik TV subscriptions. TELUS reserves the right to modify channel lineups and regular pricing without notice.
1 UNITED STATES DISTRICT COURT - Cloud Object …
s3.amazonaws.comthat Naruto is the author of the Monkey Selfies and are not required to allege “anything else” to demonstrate his standing. Id. at 7.
Managerial Accounting - Amazon S3
s3.amazonaws.comWe show the fundamental differences between managerial and financial accounting in the chart and video. ... Financial accounting Managerial accounting Users
Amazon, Financial, Accounting, Amazon s3, Managerial, Managerial accounting, Financial accounting managerial accounting
Errata for the 10th Printing of Understanding Digital ...
s3.amazonaws.comErrata for the 10th Printing of "Understanding Digital Signal Processing, 2/E", by Richard Lyons I beg your pardon for the typographical errors in the book.
Understanding, Processing, Signal, Digital, Understanding digital signal processing, Understanding digital
Errata for the 1st Printing of Understanding Digital ...
s3.amazonaws.com"Understanding Digital Signal Processing, 2/E", by Richard Lyons I beg your pardon for the typographical errors in this 1st edition.
Understanding, Processing, Signal, Digital, Understanding digital signal processing, Understanding digital
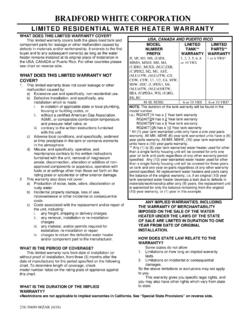
LIMITED RESIDENTIAL WATER HEATER WARRANTY
s3.amazonaws.comWHAT WILL WE DO TO CORRECT PROBLEMS? If a defect occurs within the warranty period, we will: 1. Provide a replacement water heater of our manufacture (or
Water, Replacement, Heaters, Water heaters, Replacement water heater
Welcome Coming Up March 18, 2018
s3.amazonaws.comQuartz Mountain Resort near Lone Wolf, Oklahoma. $125 and up. Register at our table in the Main Hall this morning or online at gracechurch.com/men. Elder Candidate Input
BODYWEIGHT STRENGTH TRAINING ANATOMY PDF
s3.amazonaws.comRead Online Now bodyweight strength training anatomy Ebook PDF at our Library. Get bodyweight strength training anatomy PDF file for free from our online library
Training, Anatomy, Strength, Bodyweight strength training anatomy, Bodyweight, Bodyweight strength training anatomy pdf
Related documents
Pulse Policy Secure - pulsesecure.net
www.pulsesecure.netPulse Policy Secure provides visibility into the network by detecting and continuously monitoring ... reduces threats from unauthorized users and compromised devices. Pulse Policy Secure also offers sponsored-based guest access, where ... Airwatch, and Microsoft . 4
Policy, Devices, Pulse, Secure, Detecting, Airwatch, Compromised, Compromised devices, Pulse policy secure
Detecting Compromised Devices - AirWatch
www.air-watch.comDetecting Compromised Devices with AirWatch AirWatch’s solution spans the entire life of an enrolled device, locking out uninvited devices and severing ties with compromised or non-compliant devices.
Devices, Detecting, Airwatch, Compromised, Detecting compromised devices airwatch, Detecting compromised devices, Airwatch airwatch
Implementation: Apple iOS 7+ with Xamarin - AppConfig
appconfig.orgThe EMM system is responsible for detecting and taking remediation action on a device that has been compromised or jailbroken that may expose the managed configurations. As a best practice, sensitive information such as passwords or certificates ... AirWatch Specific Setup
App Configuration for Enterprise ACE - storage.googleapis.com
storage.googleapis.comdetecting and taking remediation action on a device that has been compromised or jailbroken that may expose the managed ... AirWatch Specific Setup ... App Configuration for Enterprise | v.Mar
Configuration, Enterprise, Detecting, Airwatch, Compromised, App configuration for enterprise
The Forrester Wave™: Identity-As-A-Service, Q4 2017
www.centrify.comsecurity teams to take feeds from the IDaaS vendors about compromised accounts, websites, and IP addresses and use them in detecting, alerting, and preventing unauthorized employee or customer access to the firm’s critical properties: external website, internal apps, mobile devices, etc.
Tenable Network Security and Ingram Micro
usa.ingrammicro.comTenable Network Security and Ingram Micro ... Tenable’s Nessus vulnerability scanner, the global standard in detecting and assessing network data, simplifies vulnerability assessment, auditing, reporting and PCI compliance. ... traffic and detects devices on your network, including virtual and cloud-based devices.
Devices, Security, Network, Micro, Margin, Detecting, Benlate, Tenable network security and ingram micro