Senior Citizens and Cybersecurity Awareness - nova.edu
Introduction Billions of dollars in losses accrued to Internet users due to cyber-attacks that exploit human vulnerabilities (Abawajy, 2014).
Tags:
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
PREPOSITIONS - Nova Southeastern University
www.nova.eduPrepositions for Time, Place, and Introducing Objects Time On is used with days. I will see you on Monday. The week begins on Sunday. At is used with noon, night, midnight, and with the time of day.
University, Time, Prepositions, Nova southeastern university, Nova, Southeastern
Exercise on Identifying Triggers
www.nova.edu139 Exercise on Identifying Triggers (page 2 of 3) EXERCISE Describe two general types of situations that have triggered the behavior you want to change. One thing that can help you to identify triggers and consequences related to changing is to think about
Identifying, Exercise, Exercise on identifying triggers, Triggers
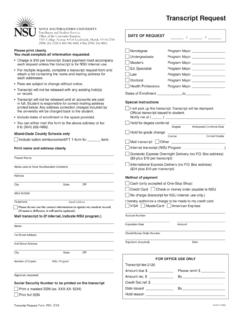
Transcript Request - Nova Southeastern University
www.nova.eduPlease print clearly. Nondegree You must complete all information requested. •Charge is $10 per transcript. Exact payment must accompany each request unless the transcript is for NSU internal use.
University, Request, Transcript, Nova southeastern university, Nova, Southeastern, Transcript request
VERBALS (Gerunds, Participles, Infinitives)
www.nova.eduVERBALS (Gerunds, Participles, Infinitives) Gerunds A gerund is a verbal that ends in –ing and functions as a noun. It can take on the role of a subject, direct object, subject complement, and object of preposition.
2013 Final Motivational Techniques and Skills
www.nova.eduMotivational)Techniques)and)Skills)) ) 1)! Sobell!and!Sobell!©2013.!Availableonlineat!http://www.nova.edu/gsc/online_files.html.!This!document!is!not!tobe!copied!or!
2017-2018 Undergraduate Academic Catalog
www.nova.eduNova Southeastern University Undergraduate Student Catalog 2017–2018 Abraham S. Fischler College of Education College of Arts, Humanities, and Social Sciences
Social, 2017, Catalog, University, Academic, 2018, Undergraduate, Nova southeastern university, Nova, Southeastern, 2017 2018 undergraduate academic catalog
THERAPIST HANDOUT 3.1 Objectives, Materials …
www.nova.edu56 Objectives, Materials Needed, Procedures, and Client Handouts (page 2 of 2) uPurpose of assessment: To gather information on presenting problem(s). uFor clients who will be participating in group therapy, discuss any concerns about being in a therapy
CONSENTIMIENTO Y ACUERDO DE SERVICIOS …
www.nova.eduCentro de servicios de Psicología CONSENTIMIENTO Y ACUERDO DE SERVICIOS PSICOLOGICOS PARA EL CLIENTE Por favor, lea atentamente la siguiente información.
GROUP QUESTIONNAIRE as you answer the …
www.nova.eduName: Date:_____ GROUP QUESTIONNAIRE • Read each statement carefully and as you answer the questions think of the group as a whole. • For each statement fill in the box under the MOST APPROPRIATE heading that best describes
Subject Verb Agreement - Nova Southeastern …
www.nova.eduSUBJECT-VERB AGREEMENT A subject is a noun or pronoun. A verb is the action performed by the subject. Matching Subjects with Verbs Verbs must agree with subjects in number and in person (1st/2nd/3rd).
Agreement, Subject, Verb, Nova, Southeastern, Subject verb agreement, Nova southeastern
Related documents
Chapter 9: Network and Internet Security
www.oakton.edunetwork and Internet security. 2. List several examples of unauthorized access and unauthorized use. 3. Explain several ways to protect against unauthorized access ... _____ controls access to a computer from the Internet and protects programs installed on a computer from accessing the Internet without authorization from the user.
Security, Network, Computer, Internet, Network and internet security
My HP Pavilion PC - HP® Official Site
h10032.www1.hp.comNorton Internet Security ... computer and ready for you to use. Keep Current • Monitor the security of your computer with the ... My HP Pavilion PC Thank you for purchasing an HP Pavilion PC. Explore many of the features of your new PC, and learn about additional products and services to ...
Security, Computer, Internet, Pavilion, Internet security, My hp pavilion pc
Quick Start Guide - Trend Micro Internet Security
solutionfile.trendmicro.comQuick Start Guide PC, Mac, Android & iOS. 01 To download the installer, open the ... monthly security report, click Yes. Access the different features ... see how your software has kept you safe Use your subscription to protect another PC, Mac, Android, or iOS device Scan your computer for threats and to Omptimize its performance Check the ...
Guide, Security, Computer, Quick, Start, Quick start guide, Internet, Internet security
Computer and Internet Security Presentation
scis.nova.edu10/17/13 2 What is Computer and Internet Security ! Computer Security " Protecting computers, information, and services from unauthorized access, change or destruction. " Internet security extends this concept to systems that are connected to the Internet
Security, Computer, Presentation, Internet, Internet security, Computer security, Computer and internet security presentation, Computer and internet security
COMPUTER INTERNET SECURITY TXGenWeb Conference
www.txgenweb.orgcomputer internet security. How vulnerable are you? A computer virus is a small program written to alter the way a computer operates, without the permission or knowledge of the user. A virus must meet two criteria: • • It must execute itself. It will often place its
Type of Security Threats and It’s Prevention
www.ijcta.comSecurity is a branch of computer technology known as information security as applied to computers and networks. The objective of online security includes protection of
Security, Computer, Threats, Types, Prevention, Type of security threats and it s prevention
Network Security Basics - SciTech Connect
scitechconnect.elsevier.comAttack In the context of computer/network security, an attack is an attempt to access resources on a computer or a network without authorization, or to bypass security measures that are in place.
Chapter 1 What is Computer Security?
www.cse.psu.edu5 Security Center, the official evaluator for the Defense Department, maintains an Evaluated Products List of commercial systems that it has rated according to the Criteria. The Criteria is a technical document that defines many computer security concepts and …
Getting Started - Webroot
download.webroot.comGetting Started. Thank you. Thank you for not giving up on the security industry. Thank you for refusing to accept mediocre. Thank you for trusting us to create ... Install Webroot SecureAnywhere on your computer Getting Started with Webroot SecureAnywhere Your keycode is …
Security, Computer, Getting, Started, Getting started, Computer getting started
Computer Networking and Management Lesson 1 Computer ...
www.science.smith.eduThe public internet is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world. Most of these computing devices …
Computer, Management, Lesson, Internet, Networking, Computer networking and management lesson
Related search queries
Network and Internet security, Computer, Internet, My HP Pavilion PC, Internet security, Security, Quick Start Guide, Computer and Internet Security Presentation, Computer and Internet Security, Computer security, Computer internet security, Type of Security Threats and It’s Prevention, Network security, Getting Started, Computer Getting Started, Computer Networking and Management Lesson