A Case Study of the Capital One Data Breach (Revised)
improve their cyber security controls for the protection of organizations and individuals. 1. Introduction . Technology is nowadays one of the main enablers of digital transformation The use of worldwide. ... imposing bigger penalties for violating privacy laws, as well as using
Tags:
Security, Capital, Cyber, Cyber security, Capital one, Bigger
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Wireless Communications and Networks
web.mit.edu4 MIT Physical layer •The physical layer plays a very important role in wireless network because it has severe limitation on transmissions Uplink with respect to downlink
Network, Communication, Wireless, Wireless communications and networks
The Aleph - MIT
web.mit.eduThe Aleph by Jorge Luis Borges O God! ... He read me many other stanzas, each of which also won his own approval and elicited his lengthy explications.
Finite Element Method
web.mit.eduRobert Cook, Finite Element Modeling For Stress Analysis, John Wiley & Sons, 1995 Introduction to Finite Element Method, http://210.17.155.47 (in Korean)
Finite Element Analysis
web.mit.eduFinite Element Analysis David Roylance Department of Materials Science and Engineering Massachusetts Institute of Technology Cambridge, MA 02139 February 28, …
Analysis, Technology, Institute, Massachusetts, Elements, Finite, Finite element analysis, Massachusetts institute of technology
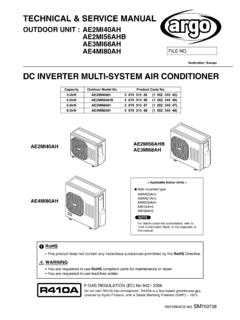
TECHNICAL & SERVICE MANUAL - MIT
web.mit.eduwhen wiring electrical shock can cause severe personal injury or death. only a qualified, experienced electrician should attempt to wire this system.
Services, Manual, Technical, Wiring, Technical amp service manual
Chapter 21 Rigid Body Dynamics: Rotation and …
web.mit.eduChapter 21 Rigid Body Dynamics: Rotation and ... patience to the establishment of the laws of rotation of the solid ... general treatment of mechanics, ...
Dynamics, Rigid, Mechanics, Body, Solid, Rotation, Rigid body dynamics, Rotation and
5.33 Lecture Notes: Introduction To Polymer …
web.mit.edu5.33 Lecture Notes: Introduction To Polymer Chemistry Polymer: A large molecule (macromolecule) built up by repetitive bonding (covalent) of smaller molecules (monomers) • Generally not a well defined structure, or molecular weight.
UNDERSTANDING, FINDING, & ELIMINATING …
web.mit.edua Senior Member of the Institute of Electrical and Electronic Engineers. CEDIA EST016 UNDERSTANDING, ... GROUNDING, AC POWER, AND SAFETY ...
PRESENTED AT THE 2004 AMERICAN CONTROL …
web.mit.eduPRESENTED AT THE 2004 AMERICAN CONTROL CONFERENCE 1 Internal and External Op-Amp Compensation: A Control-Centric Tutorial ... circuit operational …
American, Internal, Operational, Control, Conference, Compensation, Tutorials, Centric, American control conference 1 internal, A control centric tutorial
Frank and Lillian Gilbreth and the Manufacture and ...
web.mit.eduFrank and Lillian Gilbreth and the Manufacture ... time study, despite its ... publicizing micro-motion study as an advance over time study and as an
Study, Time, Manufacture, Motion, Frank, Time study, Motion study, Frank and lillian gilbreth and the manufacture, Lillian, Gilbreth
Related documents
Darktrace Antigena: Product Overview
www.darktrace.comSecurity teams in the digital age are overwhelmed, under-resourced, and ill-prepared for the shape of things to come. Cyber-threats have become increasingly automated and unpredictable, and digital environments have become more complex and diverse. Together, these trends have ... the bigger picture and influence an organization’s security ...
Security, Cyber, Bigger, Darktrace, Darktrace antigena, Antigena
Big Data: Issues and Challenges - University of Hawaiʻi
scholarspace.manoa.hawaii.educontinuum, from small data, to bigger data, to big data depending on the magnitude of each of the 3 V’s [4]. ... Compliance and Security 12 (12.9%) Structured and Unstructured Data 10 (10.8%) ... monitoring systems pose serious challenges for cyber operations because an ever growing number of devices
FIN-2020-A006 October 1, 2020 Advisory on Ransomware and ...
www.fincen.govOct 01, 2020 · • Cyber and Security Departments • Customer Service Agents • Bank Tellers FIN-2020-A006 October 1, 2020 SAR Filing Request: FinCEN requests financial institutions reference this advisory in SAR field 2 (Filing Institution ... larger enterprises to demand bigger payouts ...
The Future Of Work: Productive Anywhere | Accenture
www.accenture.comcomputing, cyber security, robotics, virtual reality and digital collaboration tools. Strong social bonds at work: The extent to which people feel connected to others and included as part of a strong social network at work. Work-life enhancement: The extent to which people feel their work enhances their energy
New Zealand's Support for Small Business
www.business.govt.nzSmart to make sure that cyber security is up to scratch. NZ CUSTOMS SERVICE Get help for your business to expand into overseas markets, including guidance on export and import procedures. WORK AND INCOME A range of services and initiatives to support employers and clients. Access their recruitment service and get matched with the right employees.
2020 China Military Power Report - U.S. Department of Defense
media.defense.govSep 01, 2020 · serious implications for U.S. national interests and the security of the international rules-based order. Report scope: This report covers security and military developments involving the PRC until the end of 2019. Developments in 2020, including the implications of the COVID-19 pandemic, will be covered in DoD’s 2021 report.
Hacking Databases for Owning your Data - Black Hat
www.blackhat.comArgeniss – Information Security Abstract: Data theft is becoming a major threat, criminals have identified where the money is. In the last years many databases from fortune 500 companies were compromised causing lots of
Database, Security, Your, Data, Hacking, Hacking databases for owning your data, Owning
Security Risk Management - Approaches and …
revistaie.ase.ro228 Informatica Economică vol. 15, no. 1/2011 Security Risk Management - Approaches and Methodology . Elena Ramona STROIE, Alina Cristina RUSU . Academy of Economic Studies, Bucharest, Romania
Security, Management, Risks, Methodology, Approaches, Security risk management approaches and, Security risk management approaches and methodology
Cyber Crime: Challenges and its Classification
www.ijettcs.orgInternational Journal of Emerging Trends & Technology in Computer Science (IJETTCS) Web Site: www.ijettcs.org Email: [email protected] Volume 3, Issue 6, November-December 2014 ISSN 2278-6856 Volume 3, Issue 6, November-December 2014 Page 120 D.Cyber attacks have come not only from terrorists but
PHILIPPINE ECONOMIC ZONE AUTHORITY - …
www.investphilippines.infoLilia B. de Lima Undersecretary and Director General Philippine Economic Zone Authority AmCham Hall, 2F, Corinthian Plaza Bldg., Paseo de Roxas, Makati City