www.dni.gov
NATIONAL INSIDER THREAT POLICY The National Insider Threat Policy aims to strengthen the protection and safeguarding of classified information by: establishing common expectations; institutionalizing executive branch
Tags:
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
The National Intelligence United States of America …
www.dni.govThe National Intelligence Strategy of the United States of America 2014. The National Intelligence Strategy of the United States of America. 1 Foreword James R. Clapper Director of National Intelligence I’ve often said publicly that we are facing the most diverse set of threats I’ve seen in my 50 years in the intelligence business. That’s true. …
United, States, Intelligence, National, Strategy, America, United states of america, National intelligence strategy
GUIDEINSIDER THREAT - dni.gov
www.dni.govinsider threat programs consistent with mission needs. While every D/A with access to classified information must adhere to the requirements set forth in the Policy & Standards, the NITTF realizes that this effort cannot have a “one size fits all” approach.
GUIDEINSIDER THREAT - DNI
www.dni.govthe insider threat mission is a dynamic effort requiring constant evaluation, fresh perspectives, and updated approaches.
Global Trends 2015 - DNI
www.dni.gov13 December 2000 From the Director of Central Intelligence I am pleased to introduce Global Trends 2015, which takes a look at the world over the next 15 years from the perspective of the national security policymaker.
GLOBAL TRENDS PARADOX PROGRESS - dni.gov
www.dni.govPARADOX O F PROGRESS A publication of the National Intelligence Council GLOBAL TRENDS JANUARY 2017 E/ îìíósììí ISBN 978-0-16-093614-2 To view electronic version:
Global, Trends, National, Council, Global trends, The national, Council global trends
INTELLIGENCE COMMUNITY POLICY GUIDANCE
www.dni.govintelligence community policy guidance number 704.2 personnel security adjudicative guidelines for determining eligibility for access to sensitive compartmented information
Policy, Intelligence, Guidance, Community, Intelligence community policy guidance
Background to “Assessing Russian Activities and …
www.dni.govThis report is a declassified version of a highly classified assessment; its conclusions are identical to those in the highly classified assessment but this version does not include the full supporting information on key elements of the influence campaign.
Status Report on the Implementation of - dni.gov
www.dni.gov3 Status Report on the Implementation of Executive Order 13698 Hostage Recovery Activities Introduction This National Counterterrorism Center (NCTC) report evaluates U.S. Government (USG)
Report, Implementation, Status, Status report on the implementation of
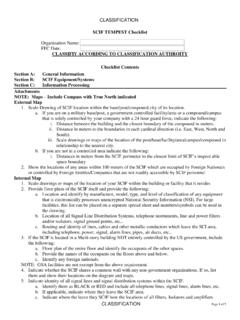
SCIF TEMPEST Checklist CLASSIFIY ACCORDING TO ...
www.dni.govPage 1 of 7 SCIF TEMPEST Checklist Organization Name: FFC Date: CLASSIFIY ACCORDING TO CLASSIFICATION AUTHROITY Checklist Contents . Section A: General Information
Checklist, Classification, According, Authority, Tempest, Classifiy according to classification authroity checklist, Classifiy
2016 - dni.gov
www.dni.govProtect Your Organization... 3 The steps to reduce the risk can be low-cost and include practical changes to current management practices that are drawn …
Related documents
Military Intelligence Threat Awareness and Reporting …
fas.orgContents—Continued Other considerations † 5–2, page 12 Chapter 6 Assessment of the Threat Awareness and Reporting Program, page 12 Purpose † 6–1, page 12 Counterintelligence unit responsibility † 6–2, page 12 Army service component command, Army commands, and direct reporting unit responsibility † 6–3, page 13 Appendixes
Programs, Intelligence, Threats, Reporting, Military, Awareness, Military intelligence threat awareness and reporting, Threat awareness and reporting program
Integrating Counterintelligence and Threat Awareness into ...
www.cdse.eduIntegrating CI and Threat Awareness into StudentYour Security Program, v2 Course Introduction Guide Page 2 Course Information Purpose Provide a thorough understanding of how counterintelligence and threat awareness is an essential component of a security program
Open-Source Intelligence ATP 2-22
fas.org10 July 2012 ATP 2-22.9 v Introduction Since before the advent of the satellite and other advanced technological means of gathering information, military professionals have planned, prepared, collected, and produced intelligence from publicly available
Open, Intelligence, Course, Military, Open source intelligence
Department of Defense - esd.whs.mil
www.esd.whs.milDoDD 5240.06, May 17, 2011 . Change 2, 07/21/2017 2 . and the Joint Staff, the Combatant Commands, the Office of the Inspector General of the Department of Defense, the Defense Agencies, the DoD Field Activities, and all other