Guide to Effective Remediation of Network Vulnerabilities.…
days after news announcements of vulnerabilities Attacks have dramatically accelerated damage by using sophisticated technology for automatic replication, pre-identification of vulnerable hosts, and targeting ... These threats are also emerging faster than ever. In the past, the discovery/attack
Tags:
Threats, Vulnerabilities, Attacks, Vulnerabilities attacks
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Qualys API Quick Reference
www.qualys.comQualys API Quick Reference Guide Vulnerability Management and Policy Compliance API 8 Notes: “title” is required for a create request. “ids” is required for an update and delete request. comments={value}&
Guide, Reference, Quick, Qualys, Qualys api quick reference, Qualys api quick reference guide
Windows Authentication - Qualys
www.qualys.com“qualys_scanner” user to the “Domain Admins” group. Click OK to save the change. Group Policy Settings Best practice Group Policy settings for authenticated scanning of Windows systems are described below. Please consult your network administrator before making changes to
Scan VMware ESXi Hosts on vCenter User Guide
www.qualys.comScan ESXi hosts on vCenter Get Started Launch scans Now you are ready to launch a scan on your ESXi hosts through vCenter. Launch a scan like any other scan and for your target hosts choose your ESXi assets by selecting IP addresses, asset groups, asset tags. The authenticated scanning occurs for the
Guide, User, Host, Scan, Vcenter, Esxi, Esxi hosts on vcenter user guide
Qualys Patch Management Getting Started Guide
www.qualys.comInstalling Cloud Agents on Assets Downloading Installer 9 As you can see, you can provision the same key for any of the other applications in your account. Downloading Installer Click Install instructions next to Windows (.exe) or Linux (.rpm).
Qualys SAML and Azure Active Directory Integration
www.qualys.comApr 07, 2021 · Tutorial: Azure Active Directory Integration with Qualys Cloud Platform using SAML SSO In this tutorial we’ll show you how to integrate Microsoft Azure Active Directory (Azure AD) with Qualys Cloud Platform using SAML 2.0 SP-initiated SSO. Integrating Qualys Cloud Platform with Azure AD provides you with these benefits:
Web Application Scanning API - Qualys
www.qualys.comNov 12, 2021 · The Qualys Cloud Platform and its integrated Cloud Apps deliver businesses critical security in telligence continuously, enabling them to automate the full spectrum of auditing, compliance and protection for IT systems and web applications on pre mises, on endpoints and elastic clouds. For more information, please visit
Qualys CloudView User Guide
www.qualys.comapplies to EC2/VPC services and Security Group Resource Service A service is the high level grouping by functional area. Each service consists of different entities or resources. Resource A resource is an entity that you can work with. Examples include an Amazon EC2 instance, IAM User, Security Group.
Amazon, Services, Guide, User, Qualys, Qualys cloudview user guide, Cloudview
Unix Authentication - Qualys
www.qualys.comJul 28, 2020 · Using Private Keys / Certificates For successful authentication, the user account must be add ed to all target hosts along with the public key, which will be appended to the “.ssh/authorized_keys2” file in the user’s home directory. Our service must have full access to the target hosts during scanning. It ’s possible that
Services, Unix, Certificate, Authentication, Unix authentication
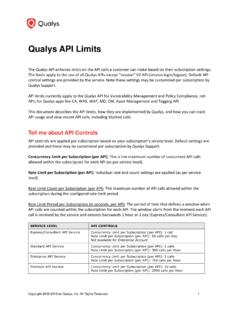
Qualys API Limits
www.qualys.comExample: 300 API calls were received starting April 12 at 2 PM. The first blocked API call was received on April 12 at 2:30 PM. Users could not run API calls for 30 minutes. The next time an API can be received and run is April 12 at 3 PM, assuming there is a maximum of 1 API call instance currently running at that time.
Qualys Gateway Service User Guide
www.qualys.comQualys Gateway Service User Interface Module 8 Qualys Gateway Service User Interface Module Qualys Gateway Service has a user interface module on the Qualys Platform. Customers with purchased or trial accounts see the QGS module in the module picker. Use the QGS UI to create, configure, monitor, disable, and delete QGS appliances deployed
Services, Guide, User, Getaways, Qualys, Qualys gateway service user guide
Related documents
Embedded Systems Security: Threats, Vulnerabilities, and ...
www.cse.psu.eduthreats and vulnerabilities. We focus on two sets of data, i.e., the exposures of attacks on embedded systems in security conferences and literature, and the published vulnerabilities specific to embedded systems. Based on the data, we derive an attack taxonomy to systematically identify and classify common attacks against embedded systems.
Security, System, Threats, Vulnerabilities, Embedded, Attacks, Embedded systems security, Threats and vulnerabilities
Wireless LAN Security Threats & Vulnerabilities
thesai.orgwireless LANs means increased danger from attacks and increased challenges to an organization, IT staff and IT security professionals. This paper discusses the various security issues and vulnerabilities related to the IEEE 802.11 Wireless LAN encryption standard and common threats/attacks pertaining to
Security, Wireless, Threats, Vulnerabilities, Attacks, And vulnerabilities, Wireless lan security threats amp vulnerabilities
Cyber Threat and Vulnerability Analysis of the U.S ...
www.energy.govMuch of the publicly available information about utilities’ vulnerabilities to cyber threats comes from reported cyber attacks, as well as the subsequent research exploring additional weaknesses and attack vectors for a particular system. Discovery, publication, and mitigation of cyber threats
COVID-19 Cyber Threats (Update)
www.hhs.gov• In recent attacks, the hackers probed for computer network vulnerabilities of entities tasked with developing COVID -19 vaccines, testing technology, and treatments. • Primarily exploited publicly known software vulnerabilities in popular web server software, web application development suites, and software collaboration programs
Threats, Attacks, and Vulnerabilities
faculty.cs.nku.eduvulnerabilities to attack systems. Vandals, hacktivists, criminals, spies, disgruntled employees, etc. Vulnerabilities are weaknesses in a system that allow a threat to obtain access to information assets in violation of a system’s security policy. Attacks are actions taken by threats to obtain assets from
Security Threats, Challenges, Vulnerability and Risks
www.eolss.netsecurity threats, challenges, vulnerabilities and risks have been reconceptualized during the 1990s and in the new millennium. Below, first the etymological origins, the synonyms and meanings of the four terms “threats, challenges, vulnerabilities and risks” in …
Guidance on Risk Analysis Requirements under the HIPAA ...
www.hhs.govJul 14, 2010 · human, and environmental. Examples of common threats in each of these general categories include: Natural threats such as floods, earthquakes, tornadoes, and landslides. Human threats are enabled or caused by humans and may include intentional (e.g., network and computer based attacks, malicious software upload, and
Common Cyber Threats: Indicators and Countermeasures
securityawareness.usalearning.govCommon Cyber Threats If you suspect you may have been a target of any of the threats included here, or have been targeted by any other cyber threat, report it to your FSO or security point of contact immediately.