Web Application Scanning - Qualys
Next scan for vulnerabilities 11 The full scan report Next scan for vulnerabilities A vulnerability scan performs vulnerability checks and sensitive content checks to tell you about the security posture of your web application. Each QID is a security check we performed and gathered information on. Just click the row to see details. Be sure to ...
Tags:
Information
Domain:
Source:
Link to this page:
Please notify us if you found a problem with this document:
Documents from same domain
Qualys Gateway Service User Guide
www.qualys.comQualys Gateway Service User Interface Module 8 Qualys Gateway Service User Interface Module Qualys Gateway Service has a user interface module on the Qualys Platform. Customers with purchased or trial accounts see the QGS module in the module picker. Use the QGS UI to create, configure, monitor, disable, and delete QGS appliances deployed
Services, Guide, User, Getaways, Qualys, Qualys gateway service user guide
Qualys API Quick Reference
www.qualys.comQualys API Quick Reference Guide Vulnerability Management and Policy Compliance API 8 Notes: “title” is required for a create request. “ids” is required for an update and delete request. comments={value}&
Guide, Reference, Quick, Qualys, Qualys api quick reference, Qualys api quick reference guide
Windows Authentication - Qualys
www.qualys.com“qualys_scanner” user to the “Domain Admins” group. Click OK to save the change. Group Policy Settings Best practice Group Policy settings for authenticated scanning of Windows systems are described below. Please consult your network administrator before making changes to
Scan VMware ESXi Hosts on vCenter User Guide
www.qualys.comScan ESXi hosts on vCenter Get Started Launch scans Now you are ready to launch a scan on your ESXi hosts through vCenter. Launch a scan like any other scan and for your target hosts choose your ESXi assets by selecting IP addresses, asset groups, asset tags. The authenticated scanning occurs for the
Guide, User, Host, Scan, Vcenter, Esxi, Esxi hosts on vcenter user guide
Qualys Patch Management Getting Started Guide
www.qualys.comInstalling Cloud Agents on Assets Downloading Installer 9 As you can see, you can provision the same key for any of the other applications in your account. Downloading Installer Click Install instructions next to Windows (.exe) or Linux (.rpm).
Qualys SAML and Azure Active Directory Integration
www.qualys.comApr 07, 2021 · Tutorial: Azure Active Directory Integration with Qualys Cloud Platform using SAML SSO In this tutorial we’ll show you how to integrate Microsoft Azure Active Directory (Azure AD) with Qualys Cloud Platform using SAML 2.0 SP-initiated SSO. Integrating Qualys Cloud Platform with Azure AD provides you with these benefits:
Web Application Scanning API - Qualys
www.qualys.comNov 12, 2021 · The Qualys Cloud Platform and its integrated Cloud Apps deliver businesses critical security in telligence continuously, enabling them to automate the full spectrum of auditing, compliance and protection for IT systems and web applications on pre mises, on endpoints and elastic clouds. For more information, please visit
Qualys CloudView User Guide
www.qualys.comapplies to EC2/VPC services and Security Group Resource Service A service is the high level grouping by functional area. Each service consists of different entities or resources. Resource A resource is an entity that you can work with. Examples include an Amazon EC2 instance, IAM User, Security Group.
Amazon, Services, Guide, User, Qualys, Qualys cloudview user guide, Cloudview
Unix Authentication - Qualys
www.qualys.comJul 28, 2020 · Using Private Keys / Certificates For successful authentication, the user account must be add ed to all target hosts along with the public key, which will be appended to the “.ssh/authorized_keys2” file in the user’s home directory. Our service must have full access to the target hosts during scanning. It ’s possible that
Services, Unix, Certificate, Authentication, Unix authentication
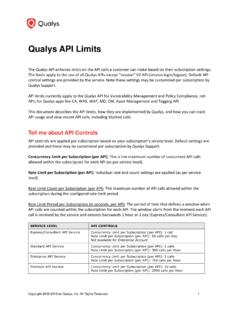
Qualys API Limits
www.qualys.comExample: 300 API calls were received starting April 12 at 2 PM. The first blocked API call was received on April 12 at 2:30 PM. Users could not run API calls for 30 minutes. The next time an API can be received and run is April 12 at 3 PM, assuming there is a maximum of 1 API call instance currently running at that time.
Related documents
Guide Symantec Endpoint Protection 14.3 RU1 for Linux Client
techdocs.broadcom.comcommand also looks for new agent packages. If an update is available, the latest kernel module is downloaded and the agent is updated automatically. After the kernel module is updated, you must restart the instance for the update to take effect. Alternatively, you can update the agent kernel module by running the following command in the instance.
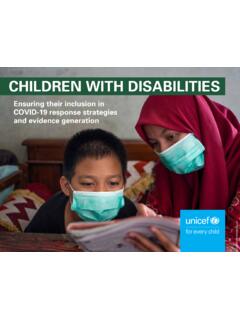
CHILDREN WITH DISABILITIES - UNICEF DATA
data.unicef.orgWashington Group Module on Child Functioning, which measures the proportion of children aged 2 to 17 years with functional difficulties in the domains of communication, hearing, vision, learning, mobility and motor skills, and emotions. By including the module, MICS has become the largest source of internationally
With, Children, Module, Disabilities, Children with disabilities
CompTIA Security+ Certification Exam Objectives
comptiacdn.azureedge.net1.0 Attacks, Threats, and Vulnerabilities 24% 2.0 Architecture and Design 21% 3.0 Implementation 25% 4.0 Operations and Incident Response 16% 5.0 Governance, Risk, and Compliance 14% Total 100% CompTIA Security+ Certification Exam Objectives Version 3.0 (Exam Number: SY0-601)
Security, Exams, Vulnerabilities, Certifications, Impacto, Comptia security certification exam
Demanded by Employers. Respected by
www.eccouncil.org(on steroids!), across 4 levels of complexity covering 18 attack vectors, including the OWASP Top 10! Covers vulnerabilities ranging from a basic cross-site script to advanced multi-level pivoting, ultimately giving access to the entire server. Learners are required to possess varied skills and procedures in order to capture the
FortiGate 80F Series Data Sheet
www.fortinet.comTrusted Platform Module (TPM) Yes Yes Yes Yes Yes Bluetooth Low Energy (BLE) Yes Yes Yes Yes Yes System Performance — Enterprise Traffic Mix IPS Throughput 2 1.4 Gbps NGFW Throughput 2, 4 1 Gbps Threat Protection Throughput 2, 5 900 Mbps System Performance Firewall Throughput (1518 / 512 / 64 byte UDP packets) 10/10/7 Gbps
HIPAA Security Series #4 - Technical Safeguards
www.hhs.govApr 20, 2005 · Volume 2 / Paper 4 3 5/2005: rev. 3/2007 STANDARD § 164.312(a)(1) NOTE: For more information on Information Access Management, see paper 2 in this series, “Security Standards – Administrative Safeguards.” NOTE: A covered entity must establish a balance between the identifiable risks and vulnerabilities to EPHI, the cost
Technical, Vulnerabilities, Safeguards, Technical safeguards
Module 5 Providing Psychosocial Support Services for ...
files.icap.columbia.eduADOLESCENT HIV CARE AND TREATMENT – PARTICIPANT MANUAL MODULE 5–4 Figure 5.1: Support needs of ALHIV Note: This figure was adapted from: Uganda Ministry of Gender, Labour, and Social Development. (2005). Integrated care for orphans and other vulnerable children: A training manual for community service providers.
Services, Psychosocial, Support, Module, Providing, Module 5 providing psychosocial support services for
Guide Symantec Endpoint Protection 14.3 RU2 for Linux …
techdocs.broadcom.comHardware • Intel Pentium 4 (2 GHz) or later processor • 500 MB of free RAM (4 GB of RAM is recommended) • 2 GB available disk space if /var, /opt, and /tmp share the same filesystem/volume • 500 MB available disk space in each /var, /opt, and /tmp if on different volumes Operating systems • Amazon Linux 2 • CentOS 6, 7, 8 • Debian ...
Protection, Endpoint, Symantec, Symantec endpoint protection 14, 3 ru2 for
Automotive Gateway: A Key Component to Securing the ...
www.nxp.com4 Looking to the Future Connected cars are like mobile devices: always-connected devices with increasing complexity, performance, and security requirements. Future autonomous vehicles’ ECUs must work together to sense, process, and act to drive. This requires moving and processing a tremendous amount of data securely between ECUs. Connected ...